A new variant of the Dharma Ransomware was released this week that appends the .brrr extension to encrypted files. This variant was first discovered by Jakub Kroustek who tweeted a link to the sample on VirusTotal.
Below I have outlined how this ransomware infects a computer, what happens when your files become encrypted, and how to protect yourself.
Unfortunately, there is no way to decrypt files infected with the Dharma Brrr Ransomware variant for free. For those who wish to discuss this ransomware or receive support, you can use our dedicated Dharma Ransomware Support & Help topic.
Distributed through hacked Remote Desktop Services
The Dharma Ransomware family, including this Brrr variant, is manually installed by attackers who hack into Remote Desktop Services connected directly to the Internet. These attackers will scan the Internet for computers running RDP, usually on TCP port 3389, and then attempt to brute force the password for the computer.
There are also underground sites that sell known credentials for publicly accessible computers running remote Remote Desktop Services that attackers can buy.
Once they gain access to the computer they will install the ransomware and let it encrypt the computer. If the attackers are able to encrypt other computers on the network, they will attempt to do so as well.
How the Brrr Dharma Ransomware encrypts a computer
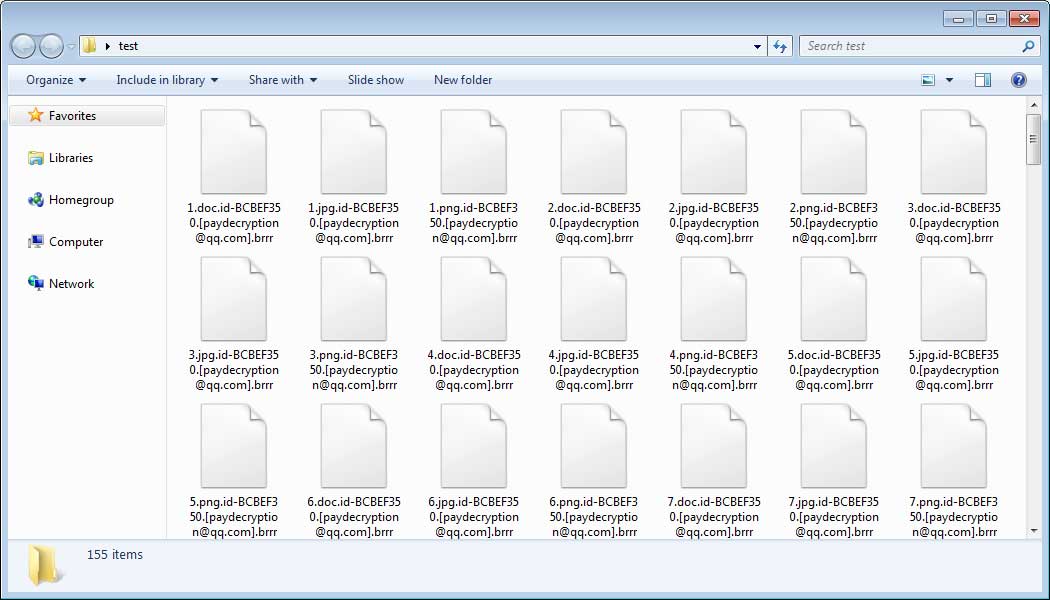
When the Brrr ransomware variant is installed on a computer, it will scan it for files and encrypt them. When encrypting a file it will append an extension in the format of .id-[id].[email].brrr. For example, a file called test.jpg would be encrypted and renamed to test.jpg.id-BCBEF350.[paydecryption@qq.com].brrr.
It should be noted that this ransomware will encrypt mapped network drives, shared virtual machine host drives, and unmapped network shares. So it is important to make sure your network’s shares are locked down so that only those who actually need access have permission.
You can see an example of a folder encrypted by the Brrr Ransomware variant below.
When encrypting files, the ransomware will create two different ransom notes on the infected the computer. One is the Info.hta file, which is launched by an autorun when a user logs into the computer. The HTML version of the ransom note can be seen below.

The other note is called FILES ENCRYPTED.txt and can be found on the desktop.
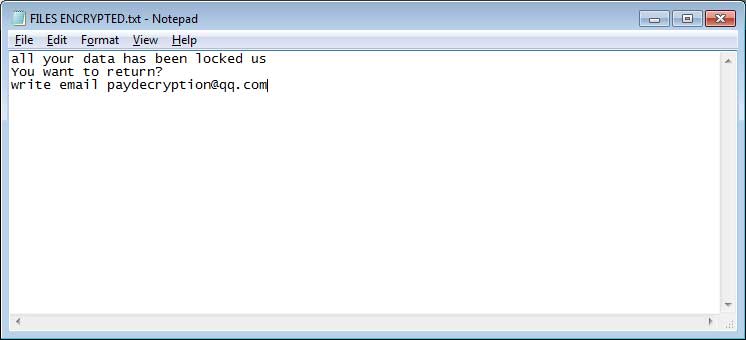
Both of these ransom notes contain information on what happened to the victim’s files and how to contact paydecryption@qq.com in order to get payment instructions.
Finally, the ransomware will configure itself to automatically start when you login to Windows. This allows it to encrypt new files that are created since it was last executed.
Once again, at this time there is no way to decrypt files infected with the Dharma Brrr Ransomware variant for free. For those who wish to discuss this ransomware or receive support, you can use our dedicated Dharma Ransomware Support & Help topic.
How to protect yourself from the Dharma Brrr Ransomware
In order to protect yourself from Dharma, or from any ransomware, it is important that you use good computing habits and security software. First and foremost, you should always have a reliable and tested backup of your data that can be restored in the case of an emergency, such as a ransomware attack.
As the Dharma Ransomware is typically installed via hacked Remote Desktop services, it is very important to make sure its locked down correctly. This includes making sure that no computers running remote desktop services are connected directly to the Internet. Instead place computers running remote desktop behind VPNs so that they are only accessible to those who have VPN accounts on your network.
It is also important to setup proper account lockout policies so that it makes it difficult for accounts to be brute forced over Remote Desktop Services.
You should also have security software that incorporates behavioral detections to combat ransomware and not just signature detections or heuristics. For example, Emsisoft Anti-Malware and Malwarebytes Anti-Malware both contain behavioral detection that can prevent many, if not most, ransomware infections from encrypting a computer.
Last, but not least, make sure you practice the following good online security habits, which in many cases are the most important steps of all:
- Backup, Backup, Backup!
- Do not open attachments if you do not know who sent them.
- Do not open attachments until you confirm that the person actually sent you them,
- Scan attachments with tools like VirusTotal.
- Make sure all Windows updates are installed as soon as they come out! Also make sure you update all programs, especially Java, Flash, and Adobe Reader. Older programs contain security vulnerabilities that are commonly exploited by malware distributors. Therefore it is important to keep them updated.
- Make sure you use have some sort of security software installed.
- Use hard passwords and never reuse the same password at multiple sites.
- If you are using Remote Desktop Services, do not connect it directly to the Internet. Instead make it accessibly only via a VPN.
For a complete guide on ransomware protection, you visit our How to Protect and Harden a Computer against Ransomware article.
To read the original article:
https://www.bleepingcomputer.com/news/security/new-brrr-dharma-ransomware-variant-released/
