Ancestry.com said it closed portions of its community-driven genealogy site RootsWeb as it investigated a leaky server that exposed 300,000 passwords, email addresses and usernames to the public internet.
In a statement issued over the weekend, Chief Information Security Officer of Ancestry.com Tony Blackham said a file containing the user data was publicly exposed on a RootsWeb server.
“Approximately 55,000 of these were used both on RootsWeb and one of the Ancestry sites, and the vast majority of those were from free trial or currently unused accounts. Additionally, we found that about 7,000 of those password and email address combinations matched credentials for active Ancestry customers,” Blackham wrote.
On Wednesday, Ancestry.com told Threatpost it believed the data was exposed on November 2015. The data resided on RootsWeb’s infrastructure, and is not linked to Ancestry.com’s site and services. Ancestry.com said RootsWeb has “millions” of members who use the site to share family trees, post user-contributed databases and host thousands of messaging boards.
The company said RootsWeb doesn’t host sensitive information such as credit card data or social security numbers. It added, there are no indications data exposed to the public internet has been accessed by a malicious third party. The company declined to specify how and why the data was stored insecurely on the server.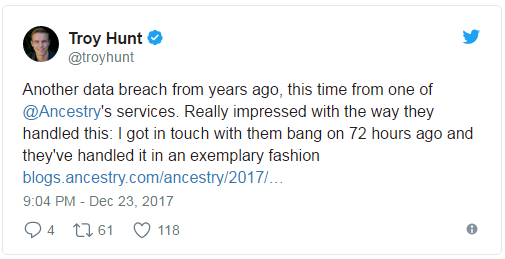
The exposure of data was first brought to Ancestry.com’s attention on Dec. 20 when Troy Hunt, who runs the data breach repository HaveIBeenPwned.com, reported to the company the existence of the file on RootsWeb’s server.
According to a tweet by Hunt the publicly exposed data contained plain text passwords.
“Our Information Security Team reviewed the details of this file, and confirmed that it contains information related to users of Rootsweb’s surname list information, a service we retired earlier this year,” Blackham said.
The company said as it investigates some of RootsWeb’s services would be taken offline. On Wednesday, visitors were greeted with the message:…
To read the original article:
https://threatpost.com/leaky-rootsweb-server-exposes-some-ancestry-com-user-data/129248/