A new ransomware called HC7 is infecting victims by hacking into Windows computers that are running publicly accessible Remote Desktop services. Once the developers gain access to the hacked computer, the HC7 ransomware is then installed on all accessible computers on the network.
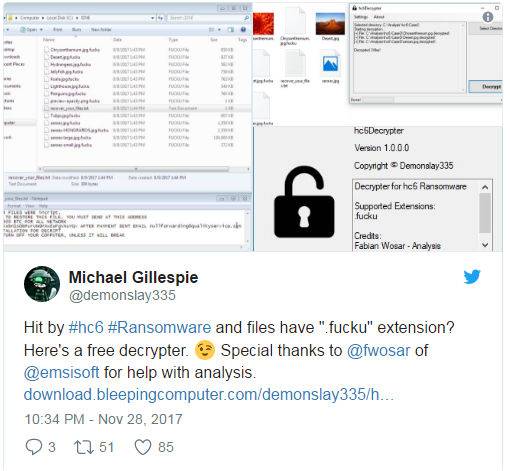
Originally released as HC6, victims began posting about it in the BleepingComputer forums towards the end of November. As this is a Python-to-exe executable, once the script was extracted ID Ransomware creator Michael Gillespie was able determine that it was decryptable and released a decryptor.
Unfortunately, a few days later, the ransomware developers released a new version called HC7 that was not decryptable. Thi sis because they removed the hard coded encryption key and instead switched to inputting the key as a command line argument when the attackers run the ransomware executable. Thankfully, there may be a way to get around that as well so that victims can recover their keys.
Attackers spreading HC7 Ransomware in network using PsExec
Currently the attackers are hacking into exposed remote desktop services, and once inside, use PsExec to install the ransomware on other computers in the network. The use of PsExec is evident in the source code below, which specifically looks for the PsExec.exe and skips it from being encrypted.
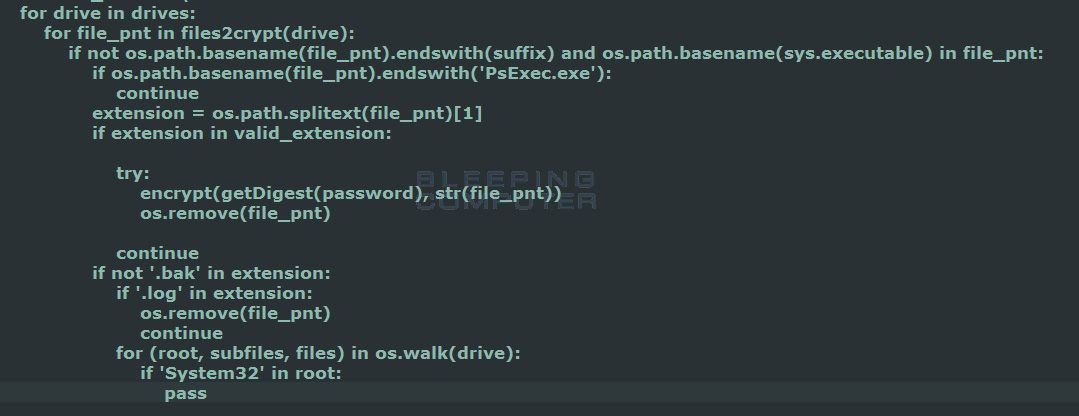
As previously stated, when the attacker executes the ransomware they will provide the encryption key as a command line argument. This key is then used to encrypt files that match the following extensions with AES-256 encryption.
To read the original article:
https://www.bleepingcomputer.com/news/security/hc7-gotya-ransomware-installed-via-remote-desktop-services-spread-with-psexec/
