Today, we at HackRead have discovered a sophisticated malware scam that tricks users into downloading fake Google Chrome browser installer but in reality, the file is infected with malware that installs Potentially Unwanted Programs (PUP’s) on Windows devices and connects to certain servers to receive commands from the remote attacker.
Google AdWords is an online advertising service that lets users pay Google to display advertisement on prominent slots during its search engine results. For instance, if the user does a Google Search using the term “Download Antivirus,” the top slot will display advertisement. In some cases first four search results display ads paid by people or companies to get quick sale or traffic.
Below is an example screenshot of Google Search Engine results that simplifies the difference between paid search and organic search results. “The top10” Free Anti-Malware 2018 result is an ad while Malwarebytes link is a result of the organic search.

In this malware scam, hackers are taking advantage of Google Adwords service and apparently paying Google to display their website link at the top. But it seems like Google does not scan links before accepting advertiser application or displaying the results to the masses.
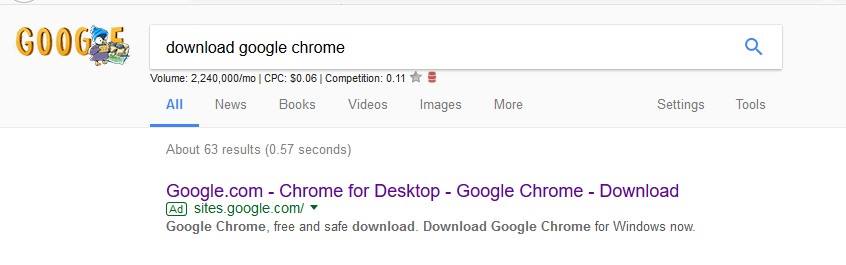
Although Google Search Results are linked to user browser cookies and/or varies from country to country, we played with “Download Google Chrome” keywords on Google and found out that the very first search result belongs to an advertiser which once clicked takes the user to a site.google.com link developed using Google Sites service.
Hackers Spreading Malware Using Google Sites
Google Sites is a structured wiki- and Web page-creation tool offered by Google as part of the G Suite productivity suite. The goal of Google Sites is for anyone to be able to create a team-oriented site where multiple people can collaborate and share files. In this case, however, once the user is on the Google Sites link it tricks users into believing that they are on the authentic Google Chrome browser download site.

To read the original article:
Hackers using Google Adwords & Google Sites to spread malware
