Anubis banking malware re-emerges again and the threat actors distributing the malware on Google Play store apps to stealing login credentials to banking apps, e-wallets, and payment cards.
Hackers always finding new ways to bypass the Google play store security and distributing malware via Android apps that will act as the first step in an infection routine that fetches the BankBot Anubis mobile banking Trojans via C&C server.
Users are frequently gets infected once they download and install the malicious apps via google play store, even though play store security inspect all the app that uploaded into Google Play, cybercriminals always implement the sophisticated techniques to evade the detection.
Researchers found anew downloaders in-app store that linked with Anubis banking malware and this campaign contains at least 10 malicious downloaders disguised as various applications.
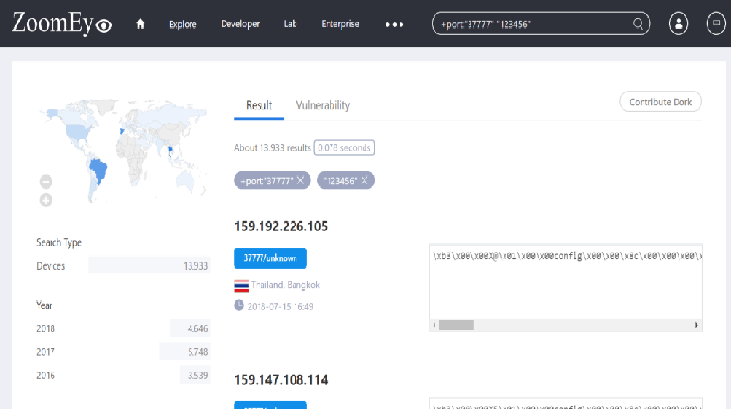
All the Downloader distributed via Android apps can fetch more than 1,000 samples from the criminal’s command-and-control (C&C) servers.
Cyber criminals uploading apps into google play store looks live a legitimate one they compromise users by promoting that they are providing “expertise” as a service.
Anubis banking malware Sample apps
Researchers discovered Malicious apps play store apps that posed as a legitimate one and the downloader apps target Turkish-speaking users.
All the malicious apps are uploaded to different categories such as online shopping to financial services and even an automotive app.

Malicious downloader is more stealthy and one of the apps contains zero detection in VirusTotal listed antivirus engines.
According to X-Force’s analysis, these changes suggest that the downloader app is being maintained on an ongoing basis — another sign that it is a commodity offered to cybercriminals or a specific group that’s focused on defrauding Turkish mobile banking users.
Once malicious downloader successfully installed into the victims Android mobile then the app fetches BankBot Anubis from one of its C&C servers.
Also, BankBot Anubis malware posed as an app called “Google Protect” and force users to grant the permission.
https://gbhackers.com/hackers-distributing-anubis-banking-malware/