Security researchers from AhnLab, a South Korea-based cyber-security firm, have created decrypters for some versions of the Magniber ransomware.
The decrypters are available for download from AhnLab’s website. Usage instructions are included in the first link.
There are no English versions for these pages, so victims will have to use an online translation service to read them, but we doubt that many English-speaking users were infected, to begin with.
Researchers deliver on their promise
The Magniber ransomware first appeared in mid-October 2017. The ransomware replaced the Cerber ransomware as the primary ransomware payload distributed via the Magnitude exploit kit.
Ever since security researchers have started tracking Magniber infections, this ransomware operation has been only focused on infecting South Korean users.
Back in October last year, several security researchers told Bleeping Computer that the ransomware appeared to be decryptable. Now, the AhnLab team has finally managed to find a chink in Magniber’s armor.
« I knew we could make a recovery tool from an encryption bug, » Cha Minseok, a security researcher with AhnLab told Bleeping Computer yesterday.
New decrypters released at regular intervals
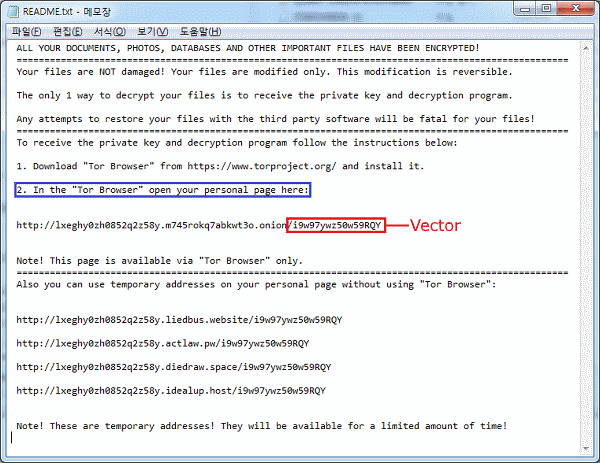
Below is a table taken from AhnLab’s website detailing what Magniber versions can be decrypted with the company’s tools.
The AhnLab team has been releasing new decrypters on almost a daily basis, so we expect this table to become outdated in a few days. For an updated one, check AhnLab’s website.
| Decrypter release date | Recoverable file extension | Victim Key | Magniber payment site vector | Download Link |
| 3/30 | kympzmzw | Jg5jU6J89CUf9C55 | i9w97ywz50w59RQY | MagniberDecrypt.zip |
| 3/30 | owxpzylj | u4p819wh1464r6J9 | mbfRHUlbKJJ7024P | MagniberDecrypt.zip |
| 3/30 | prueitfik | EV8n879gAC6080r6 | Z123yA89q3m063V9 | MagniberDecrypt.zip |
| 3/31 | rwighmoz | BF16W5aDYzi751NB | B33hQK9E6Sc7P69B | MagniberDecrypt.zip |
| 3/31 | bnxzoucsx | E88SzQ33TRi0P9g6 | Bo3AIJyWc7iuOp91 | MagniberDecrypt.zip |
| 3/31 | tzdbkjry | n9p2n9Io32Br75pN | ir922Y7f83bb7G12 | MagniberDecrypt.zip |
| 4/1 | iuoqetgb | QEsN9KZXSp61P956 | lM174P1e6J24bZt1 | MagniberDecrypt.zip |
| 4/1 | pgvuuryti | KHp4217jeDx019Uk | A4pTQ6886b401JR5 | MagniberDecrypt.zip |
| 4/2 | zpnjelt | LyAAS6Ovr647GO65 | nS3A41k9pccn03J2 | MagniberDecrypt.zip |
| 4/2 | gnhnzhu | I0727788KuT5kAqL | sCnHApaa61l5U2R0 | MagniberDecrypt.zip |
| 4/3 | hssjfbd | u5f1d693LGkEgX07 | kV35Z1K3JB7z6P06 | MagniberDecrypt.zip |
| 4/3 | ldolfoxwu | i24720y16f10qJ21 | fX5U9Z6A2j8ZUvkO | MagniberDecrypt.zip |
| 4/3 | zskgavp | nuu9WO56Gc0N5hn7 | ASY0d6dlyrEH6385 | MagniberDecrypt.zip |
| 4/3 | gwinpyizt | dcQOje3dzW469125 | T5438Nl5VI62XxM8 | MagniberDecrypt.zip |