The VPNFilter botnet that was built by Russian cyberspies, which infected over 500,000 routers, and was taken down last week by the FBI is attempting a comeback, according to telemetry data gathered this week.
Security researchers from JASK and GreyNoise Intelligence revealed on Friday that they had detected the same threat actor that built the first iteration of the VPNFilter botnet attempting to compromise new routers and build a new VPNFilter botnet.
New scans focus on Ukraine alone
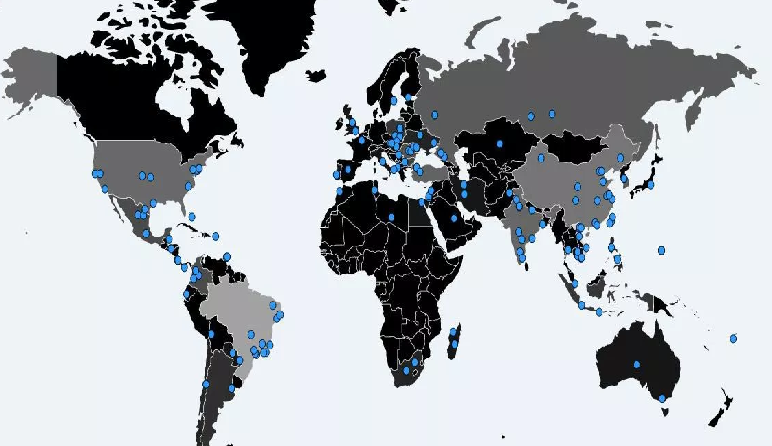
All scans looked for Mikrotik routers with port 2000 exposed online, and only routers located on Ukrainian networks.
The focus on Ukrainian routers is not a surprise for researchers. The first version of the VPNFilter botnet infected over 500,000 routers and NAS devices located all over the world, but since May 8, the botnet had started looking for Ukrainian routers in particular.
Furthermore, the old VPNFilter botnet also had a C&C server dedicated to managing Ukrainian devices alone, separately from the main botnet.
At the time of its public disclosure, security researchers believed the group behind it —the infamous APT28 Russian cyber-espionage unit— was preparing an attack on Ukraine’s IT infrastructure ahead of the UEFA Champions League final, held last Saturday, May 26.
Soon after Cisco Talos researchers revealed the botnet’s existence, the FBI stepped in and took over the domain name used to manage the VPNFilter’s command-and-control infrastructure, effectively taking over the entire botnet.
But APT28 appears to be unphased by the FBI’s takedown of its original VPNFilter botnet and is now looking for new devices to compromise, and maybe this time, get to carry out its planned attack.
The VPNFilter malware is no joke
The VPNFilter malware that infects devices is considered one of the most advanced pieces of IoT malware. The VPNFilter malware —which doesn’t have anything to do with VPNs— is comprised of three types of payloads.
The first-stage payload can achieve boot persistence on devices and survive reboot operations (the second IoT malware to ever achieve this), the second-stage component is akin to a remote access trojan (RAT), while the third-stage payloads are plugins for this RAT, which add extra functionality.
Until now, security researchers who analyzed the VPNFilter malware say this malware strain can wipe local firmware, inspect local traffic, communicate via Tor, and search for ICS device traffic on the local network by looking for Modbus-related traffic on port 502.
Ukrainian officials need to remain vigilant
Most of these features are more commonly found in nation-state malware, rather than regular IoT strains. This confirms an initial assessment from the FBI and Department of Homeland Security that Russia’s APT28 hacking group was behind the creation of this threat, rather than your regular script kiddie or cyber-criminal interested in launching DDoS attacks and proxying traffic for cash.
A report authored by the Estonian Foreign Intelligence Service claims APT28 is a unit of the Russian Military’s Main Intelligence Directorate (abbreviated GRU).
This group has been behind several cyber-attacks aimed at Ukraine in the past, such as the NotPetya ransomware outbreak, and the BlackEnergy attacks on Ukraine’s power grid in 2015 and 2016.
With a new VPNFilter rising from the ashes of the old one, Ukrainian officials will need to remain vigilant in order to thwart any cyber-attacks.
Ukraine has been the target of many cyber-attacks in the past years since its war with pro-Russian rebels started in 2014, such as the BlackEnergy incidents, NotPetya, Bad Rabbit, and PSCrypt.
To read the original article:
https://www.bleepingcomputer.com/news/security/the-vpnfilter-botnet-is-attempting-a-comeback/