According to experts at Kaspersky, the Roaming Mantis malware is designed for distribution through a simple, but very efficient trick based on DNS hijacking.
According to experts at Kaspersky, the Roaming Mantis malware is designed for distribution through a simple, but very efficient trick based on DNS hijacking.
Imagine a nefarious person swapped out your phone book with one they created, where all of the important phone numbers have been changed to call the bad actors’ friends instead of the bank you were trying to call.
Then imagine whomever answered the phone was able to convince you they actually are the bank you thought you were calling. You answer your security questions over the phone and when you hang up, the bad actor then calls your bank and successfully masquerades as you since they now have answers to your security questions. It is a flawed analogy since none of us use phone books anymore. But if you replace “phone books” with “DNS”, it is not just an analogy — it is a real cyberattack targeting mobile phone users in Asia right now — and it appears to be after users’ banking details.
In March 2018, reports began to surface about hacked routers in Japan redirecting users to compromised websites. Investigation by Kaspersky Lab indicates that the ongoing attack is targeting users in Asia with fake websites customized for English, Korean, Simplified Chinese and Japanese. Infection statistics show that users in Bangladesh, Japan and South Korea are the most impacted.
“Our research revealed that the malware (sic) contains Android application IDs for popular mobile banking and game applications in South Korea. The malware is most prevalent in South Korea, and Korean is the first language targeted in HTML and test.dex. Based on our findings, it appears the malicious app was originally distributed to South Korean targets. Support was then added for Traditional Chinese, English, and Japanese, broadening its target base in the Asian region.”
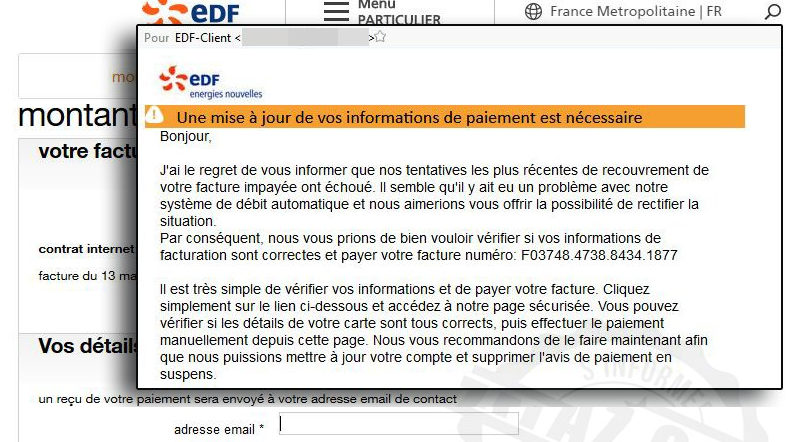
The attack begins when a user attempts to access a legitimate website through a compromised router. Instead of reaching the intended website, the user is redirected to a convincing copy of the website and will be presented with a popup dialog box which says, “To better experience the browsing, update to the latest Chrome version.” When the user clicks on the OK button, a file called chrome.apk is downloaded, but instead of containing an updated Chrome browser, the file contains the Roaming Mantis malware. During installation of the malware, the user will be prompted to authorize a number of permissions including the ability to appear on top of other applications, access the contact list, collecting account information, sending/receiving SMS messages, making phone calls, recording audio.
Once these permissions have been confirmed by the user, the next stage of the compromise begins.
Using the ability to appear on top of other applications, the malware displays a warning message that says, “Account No. exists risks, use after certification.” When the user presses the Enter button, a fake version of a Google website hosted on a temporary web server on the phone is displayed. The fake pages show the user’s Gmail ID and ask for the user’s Name and Date of Birth. This will provide the bad actors with users’ Google IDs, full names and dates of birth which is enough to start compromising banking information.
Most banks require a second authentication factor (2FA) before allowing a user to make changes, but the malware is authorized to intercept SMS messages which should subvert many 2FA processes.
Bad actors implement upgrade processes for malware to ensure they can adapt and improve over time. Roaming Mantis makes use of popular Chinese social media site my.tv.sohu.com for its command & control (C2) needs. Simply making changes to a specific user profile on the social media network can trigger updates on all infected systems. It will be very difficult for technical systems to identify malicious account updates from benign ones.
What is a user to do? It starts with securing the router. Up-to-date firmware, strong passwords for admin access and disabling remote access to the administration interfaces on the router will make it difficult to compromise. This attack targets DNS services running on routers. A DNS service running on a server inside your network is not at risk to this attack (but is not impervious to all attacks.) Only install software from trusted app stores (e.g. Google Play.) Even when installing from a legitimate app store, pay attention to the permissions that are being requested. You are being prompted to approve the permissions so you can make an informed choice. And finally, bad actors are getting much better at language translations. When you see something in your language that doesn’t sound “right” be extra suspicious.
To read the original article:
https://securityaffairs.co/wordpress/71458/malware/mantis-malware-campaign.html