Malware that embeds a null character in its code can bypass security scans performed by the Anti-Malware Scan Interface (AMSI) on Windows 10 boxes.
Microsoft fixed this vulnerability last week when it released the February 2018 Patch Tuesday security updates.
Flaw affects AMSI Windows 10 security feature
The vulnerability resides with Anti-Malware Scan Interface (AMSI), a generic security feature that acts as an intermediary point between apps and local antivirus engines.
AMSI allows an app to send a file to be scanned by the local security software and return the results. AMSI was introduced with Windows 10 and is vendor agnostic, meaning it will automatically send the file to any AMSI-compatible AV engine on the local PC, not just the built-in Windows Defender.
While AMSI can be used to scan all types of files, Microsoft specifically developed AMSI to help inspect scripts invoked at runtime, such as PowerShell, VBScript, Ruby, and others, which have become a preferred method of avoiding detection on computers using classic signature-based antivirus engines.
In other words, AMSI acts as a post-execution scanner of checks additional resources loaded or triggered by an executed file.
AMSI mishandles files containing null characters
Vancouver-based security researcher Satoshi Tanda has discovered that a bug in AMSI truncates files after a null character.
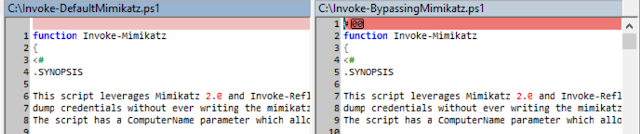
This means that AMSI will scan a file up until the null character and drop the rest of the data. An attacker only has to hide malicious commands behind a null character to bypass AMSI checks.
In a blog post with more technical details and a few examples, Tanda downloaded and ran malicious PowerShell files, but also ran malicious PowerShell commands with malicious code hidden after a null character encoded in the command itself.
« In theory, no action other than applying the patch should be required, » Tanda says. « However, software vendors using AMSI to scan PowerShell contents should review whether it can handle null characters properly should they appear. »
Tanda recommends that antivirus engines also test their own software to make sure their own scan engines aren’t truncating files that include null characters.
The bug Tanda discovered also seems to affect only AMSI’s PowerShell interface, and AMSI’s Windows Script Host interpreter does not seem to be affected.
While Tanda’s bug might seem benign, in reality, it is not. There’s been a visible trend on the malware scene in the past years, with attackers migrating to using legitimate apps to carry out malicious operations via Powershell scripts. An AMSI bypass like this can prove to be more than useful for attackers that have shifted from classic malware to this new trend of using legitimate files.
to read the original article: https://www.bleepingcomputer.com/news/security/null-character-bug-lets-malware-bypass-windows-10-anti-malware-scan-interface/
