North Korean governments sponsored & worlds most famous hacking group HIDDEN COBRA using a new Attack called “FASTCash” to cash out from the ATM Machine by compromising the bank server.
using a various mechanism to compromise and maintain the persistance in the victim’s network.
In this case, FBI & DHS issued a serious warning about this cyber attack and examines the tactics, techniques of FASTCash-Related Malware.
APT attackers initiating this ATM based attack mainly targeting against Africa and Asia based banks and still investigating this incident to confirm whether it targets any other origins.
Previous similar incidents conducted by HIDDEN COBRA hackers have stolen tens of millions of dollars and they enabled cash to be simultaneously withdrawn from ATMs located in over 30 different countries.
Another incident in this year same threat actors enable the cashout and withdraw money from ATMs in 23 different countries.
FASTCash scheme refers that an attacker remotely compromises payment switch application servers within banks to facilitate fraudulent transactions also attackers focusing on retail payment systems that vulnerable to remote exploitation.
How Does This FASTCash campaign Works
Initially, HIDDEN COBRA attackers targeting Bank employees using Spear phishing campaign in order to compromise the bank network but an exact infection vector of this campaign is still unknown.
Mainly they are using Windows-based malware to explore a bank’s network that helps to identify the payment switch application server.
Later attackers using some legitimate credentials to move further in bank network and access the switch application server using a specific pattern.
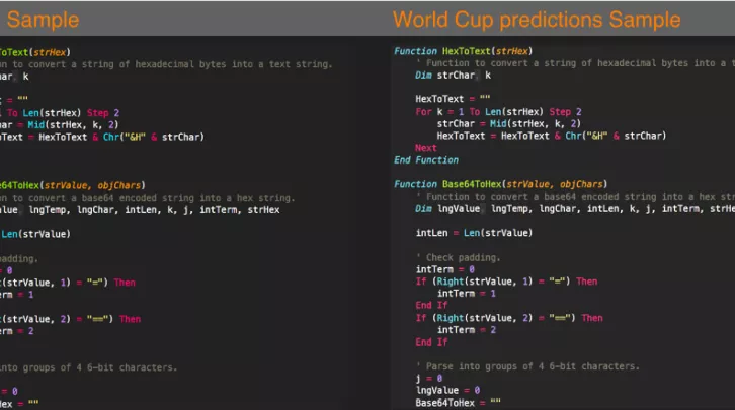
Based on the US-CERT Statement,some of the files used by HIDDEN COBRA actors were legitimate, and not inherently malicious, it is likely that HIDDEN COBRA actors used these legitimate files for malicious purposes. See MAR-1021537 for details on the files used. Malware samples obtained for analysis included AIX executable files intended for a proprietary UNIX operating system developed by IBM.
Once the bank switch application server successfully compromised then the threat actors deploy the legitimate script on the payment switch application server using command-line utility applications in order to intercept and reply to financial request messages with fraudulent but legitimate-looking affirmative response messages.

Also, the APT group has highly skilled experts who all are having extraordinary knowledge of International Standards Organization (ISO) 8583—the standard for financial transaction messaging to deployed ISO 8583 libraries on the targeted switch application servers.
This helps to interpret financial request messages and properly form a fraudulent financial response message.
Finally, the injected malicious script basically alter the expected behavior of the server by targeting the business process, rather than exploiting a technical process. US-CERT said.
In this case, “U.S. Government recommends that network administrators review MAR-10201537 for IOCs related to the HIDDEN COBRA FASTCash campaign, identify whether any of the provided IOCs fall within their organization’s network, and—if found—take necessary measures to remove the malware.”
To read the original article:
https://gbhackers.com/fastcash-attack/