Did you visit YouTube from January 18th to January 26th? There is a chance your browser was used by hackers to generate Monero cryptocurrency.
Since the value of Bitcoin has increased hackers and cybercriminals are taking advantage of every situation they can use to make easy money. This time, however, in a shocking event it has been identified that ads on Google’s YouTube, a popular video-sharing website, were using computing power (CPU) of its visitors to generate Monero cryptocurrency without their knowledge or permission.
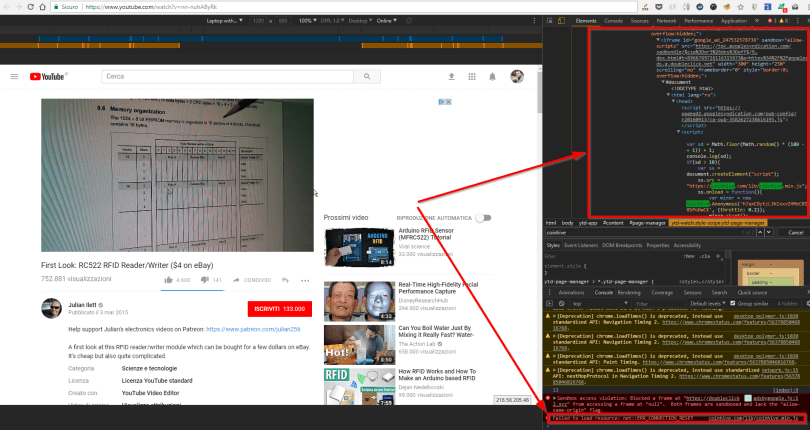
CoinHive Code On YouTube Ads
It all started on January 25th when an Italian web developer Diego Betto, Tweeted that while visiting YouTube he noticed his CPU usage suddenly increased hinting at the presence of cryptocurrency minor on the site. On further analysis, Betto found out YouTube ads were infected with CoinHive JavaScript code to mine Monero.
On the other hand, CloudFlare considers the secret use of CoinHive code as using malware against site visitors. To prove its point, the security firm booted off one of its customers in October for using the CoinHive code and not allowing users to opt out of it or disable the code.
Was YouTube Compromised?
In a conversation with ArsTechnica, YouTube acknowledged the misuse of its ads but claims that the infected ads were blocked within two hours and malicious actors were also removed from its platforms.
“Mining cryptocurrency through ads is a relatively new form of abuse that violates our policies and one that we’ve been monitoring actively. We enforce our policies through a multi-layered detection system across our platforms which we update as new threats emerge. In this case, the ads were blocked in less than two hours and the malicious actors were quickly removed from our platforms.”
To read the original article:
https://www.hackread.com/hackers-using-youtube-ads-to-mine-monero-cryptocurrency/
