Windows Server, Apache Solr, and Redis servers have been targeted this week by cyber-criminals looking to take over unpatched machines and install malware that mines cryptocurrency (known as a coinminer).
Two separate campaigns have been spotted, both very active this week. One by the Imperva crew, targeting Redis and Windows Servers, and another by the ISC SANS team, targeting Apache Solr installations.
Campaign targeting Redis and Windows Server
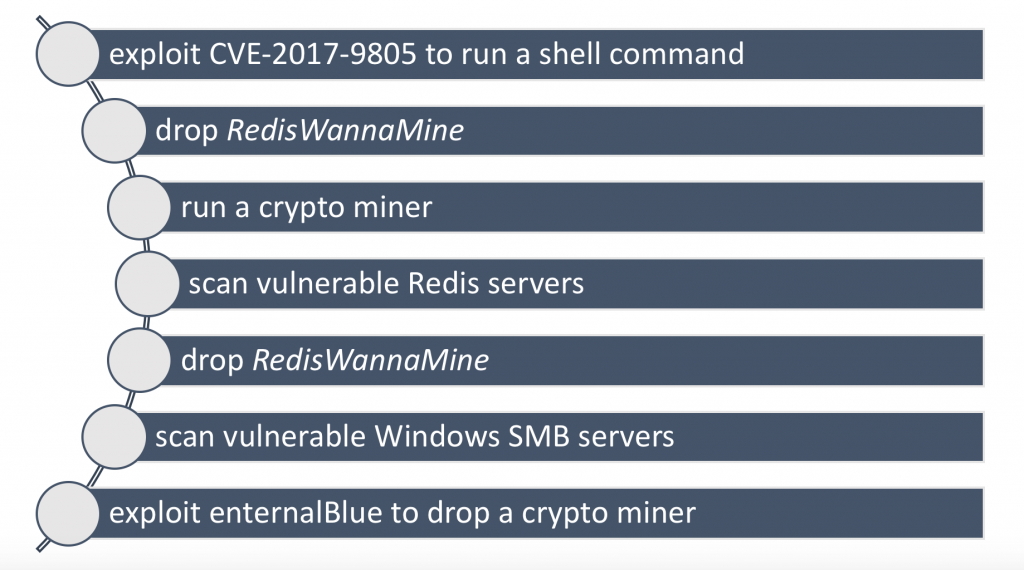
The most active of the two was a campaign that Imperva nicknamed RedisWannaMine. This campaign is ongoing, and according to Imperva, cyber-criminals have been compromising servers by mass-scanning the Internet for systems running outdated Redis versions that are vulnerable to the CVE-2017-9805 exploit.
Once criminals gain access to a host, their typical infection chain is to drop the ReddisWannaMine malware that later installs a scond-stage cryptocurrency miner.
But the ReddisWannaMine campaign also displays the classic behavioral pattern of a self-propagating worm. This is because attackers also use the same infected servers to mass-scan and later exploit other targets.
However, the ReddisWannaMine attackers aren’t only targeting other Redis servers, but are also looking for Windows Servers with exposed SMB ports.
For these latter Windows Servers instances, attackers deploy the now classic leaked NSA exploit EternalBlue. In these infections, too, they also drop a coinminer on the Windows Server machines they compromise, showing that cryptocurrency is the primary objective of these attacks.
This isn’t the first time that a coinminer campaign has targeted Redis servers. Earlier in February, another campaign made almost $1 million by infecting Redis and OrientDB servers with similar cryptocurrency mining malware.
Campaign targeting Apache Solr
But besides the ReddisWannaMine crew, there was another very active cyber-criminal group this week. This second one targeted Apache Solr servers that hadn’t received patches for the CVE-2017-12629 vulnerability.
Just like in the ReddisWannaMine incidents, attackers focused on infecting victims with a cryptocurrency miner.
ISC SANS researchers didn’t notice any self-propagation mechanism, meaning scans and infections were taking place from a central location, but they did manage to determine an approximate number of affected servers —1,777— infections that appear to have taken place between February 28 and March 8.
But while Redis and Windows Servers are standalone systems that are easier to patch, Apache Solr (search servers) are in many cases embedded in other more complex software, and patching isn’t as easy at it sounds because updating Solr might sometimes breaking internal systems that depend on it.
to read the original article :
