تم اليوم اختراق الموقع الرسمي للاهلي المصري قبل ساعات من مباراة الدور النهائي اياب لكأس رابطة الابطال الافريقية، وقد تم وضع صورة لفريق الترجي الرياضي التونسي مرفوقة بعنوان » الترجي ينتصر على الاهلي المصري بنتيجة 5 اهداف مقابل صفر. ونجح الهاكر في حذف أخر الأخبار على الصفحة الرئيسية للنادي الاهلي […]
Hacking
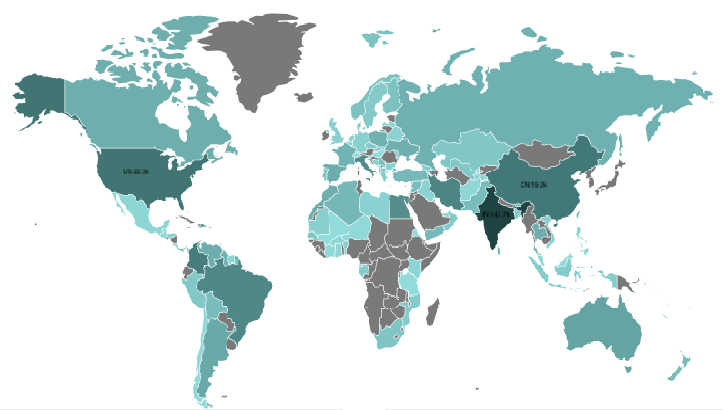
BCMPUPnP_Hunter: A 100k Botnet Turns Home Routers to Email Spammers
Since September 2018, 360Netlab Scanmon has detected multiple scan spikes on TCP port 5431, each time the system logged more than 100k scan sources, a pretty large number compared with most other botnets we have covered before. The interaction between the botnet and the potential target takes multiple steps, it starts with tcp port […]
New attack by Anonymous Italy: personal data from ministries and police have been released online
New attack by Anonymous Italy: personal data from ministries and police have been released online. The site of Fratelli d’Italia, a post-fascist party, has been defaced The iconoclastic fury of Italian Anonymous does not stop. As announced, the three groups that coordinate the operation “Black Week” have released also today new […]
Beware!! Cyber Criminals Stealing Cash From Cardless ATM Using SMS Phishing Attack
Malicious hackers stealing cash from cardless ATM using a new form of SMS phishing attack that force let user give away their bank account credentials into the phished website. Cardless ATM is now using various financial institutions to take users cash without any form of physical cards but only using […]
Intel CPUs impacted by new PortSmash side-channel vulnerability
Intel processors are impacted by a new vulnerability that can allow attackers to leak encrypted data from the CPU’s internal processes. The new vulnerability, which has received the codename of PortSmash, has been discovered by a team of five academics from the Tampere University of Technology in Finland and Technical […]
Google’s stealthy sign-in sentry can pick up pilfered passwords
Two things happened on Halloween with a bearing on cybersecurity. The first is that the 15th year of the National Cyber Security Awareness Month (NCSAM) came to an end. You have heard of NCSAM, right? The second, apparently timed to coincide with 31 October, was that Google is yet again modifying the background security […]
Cyberattaques contre les agences de voyage
Cyberattaques contre les agences de voyage: la FTAV et Amadeus en campagne de sensibilisation 111 billets d’avion pour une valeur de 350 MD émis frauduleusement par des hackers sur le dos des agences de voyage tunisiennes entre 2011 et 2018. C’est le constat amer fait par Amadeus Tunisie, principal GDS fournisseur de solutions technologiques […]
Méfiez-vous de cette arnaque très sophistiquée !
Une opération d’hameçonnage (phishing en anglais) a touché ces derniers jours un grand nombre d’utilisateurs des services de messagerie sous la forme d’un mail envoyé par un contact qui vous conseille de changer immédiatement votre mot de passe au motif qu’ il a été piraté par des hackers. Une manipulation […]
Russian hackers compromise 120 million Facebook accounts; private messages on sale online
Facebook has fallen victim to countless security breaches and November brings even more bad news for the social network. Russian hackers are selling private conversations of at least 81,000 Facebook accounts at 10 cents per account, writes the BBC. According to the BBC Russian Service, which communicated with the hackers, the criminals […]
Two Zero-Day Bugs Open Millions of Wireless Access Points to Attack
Called BleedingBit, this vulnerability impacts wireless networks used in a large percentage of enterprise companies. Two zero-day vulnerabilities in Bluetooth Low-Energy chips made by Texas Instruments (and used in millions of wireless access points) open corporate networks to crippling stealth attacks. Adversaries can exploit the bugs by simply being approximately […]