A Brazilian ISP appears to have deployed routers without a Telnet password for nearly 5,000 customers, leaving the devices wide open to abuse.
The devices have been discovered this week by Ankit Anubhav, Principal Researcher at NewSky Security, a cyber-security company specialized in IoT security.
All exposed devices are Datacom routers the ISP —Oi Internet— has provided to customers. Anubhav says he identified three types of Datacom routers —DM991CR, DM706CR, and DM991CS.
Type ENTER to hack
Some devices featured a Telnet password, but the vast majority allowed anyone to connect to the router and alter its configuration.
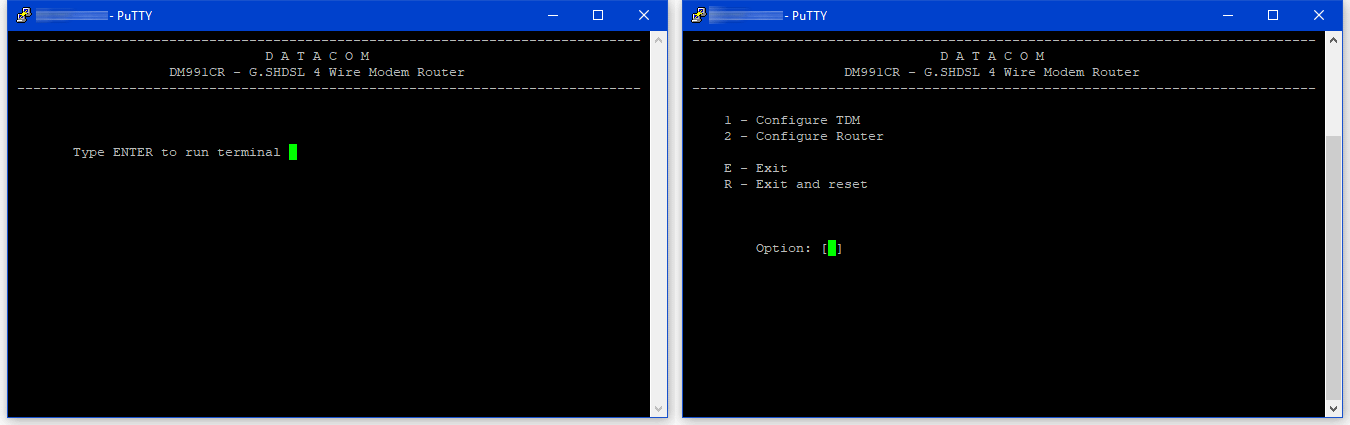
« This is not an issue with device architecture, but a poor configuration of the devices as their telnet is exposed to the outside world without any challenge, » Anubhav told Bleeping Computer earlier today.
The researcher pointed us to one of the router’s manuals which suggests the devices come with a passwordless Telnet service by default, meaning users must configure one themselves.
Bleeping Computer attempted to contact Oi Internet yesterday and today, but we were only greeted by automated chat bots and employees who didn’t speak English. NewSky Security told Bleeping Computer they have notified CERT Brazil of the exposed routers, asking the local agency to contact the ISP with their findings and come up with a solution to protect the exposed devices.
Taking over the devices is a piece of cake
Taking over these routers is a piece of cake for attackers, as they can write automated scripts that leverage the lack of a Telnet password to ensnare the exposed routers in a botnet.
« IoT attacks can be simplified to three levels: Level 0 (attacking device with no authentication), Level 1 (guessing a weak/default password), and Level 2 (using an IoT exploit to gain access), » Anubhav explains.
« While IoT attackers are becoming sophisticated with time, with NewSky Security seeing an increase in level 2 attacks, we can still observe that the easiest attack vector (using a level 0 attack of controlling a device with no authentication) is still very relevant in 2018, thanks to owners exposing their devices without even setting a password. »
« Setting up a strong password and keeping your IoT device updated limits the attackers to use either a zero-day or a lengthy bruting session, both of which are not very lucrative options for most attackers, hence making your device safe, » the expert added.
To read the original article:https://www.bleepingcomputer.com/news/security/5-000-routers-with-no-telnet-password-nothing-to-see-here-move-along/
