The experts at Yoroi-Cybaze Zlab described three techniques commonly implemented by threat actors to avoid detection. Introduction During our analysis we constantly run into the tricks cyber-attackers use to bypass companies security defences, sometimes advanced, others not. Many times, despite their elegance (or lack of it), these techniques are effective and actually […]
Année : 2019
Anonymous and LulzSec target the Italian Police and doctors
In the last 10 days, the collectives of Anonymous and LulzSec continued their operations carrying out several cyber attacks. The main objectives of the attacks carried out by Anonymous and LulzSec ITA were the Italian doctors and the Law enforcement agencies Forces, in particular, the Police and the Carabinieri. They […]
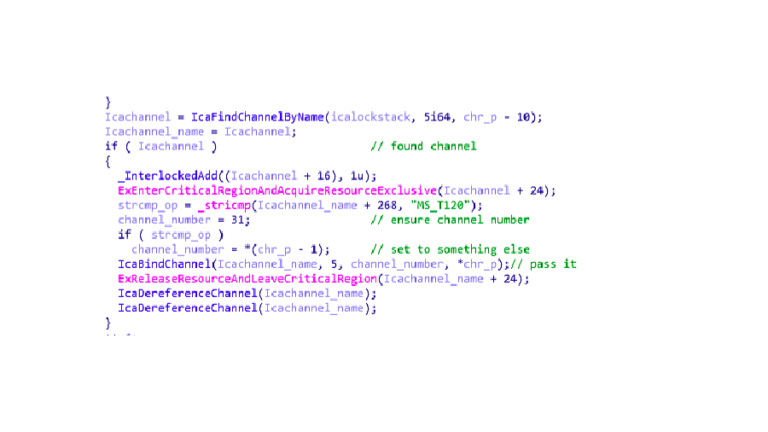
CVE-2019-0708 Technical Analysis (RDP-RCE)
CVE-2019-0708 Technical Analysis (RDP-RCE) Microsoft patch Tuesday this May (2019) comes with patch for critical RDP RCE Vulnerability, CVE-2019-0708 Remote Code Execution Vulnerability exists in Remote Desktop Services (RDP) pre-authentication and requires no user interaction Microsoft described it as “Wormable” so we could see new Wannacry hit the world ! […]
US Tech Giants Google, Intel, Qualcomm, Broadcom Break Up With Huawei
Google has reportedly suspended all businesses with the world’s second-biggest smartphone maker, Huawei, and revoked its Android license effective immediately—a move that will have a drastic impact on Huawei devices across the globe. Revoking Android license means Huawei future smartphones will no longer have access to Android updates and apps […]
Unpatched Ethereum Clients expose the ecosystem to 51% Attack risk
Security researchers from SRLabs have published a report that analyzed the risks for Ethereum network caused by unpatched Ethereum clients. Researchers at SRLabs published a report based on ethernodes.org data, that revealed that a large number of nodes using the popular clients Parity and Geth is still unpatched. The expert discovered […]
Linux kernel privilege escalation flaw CVE-2019-11815 affects RDS
Experts discovered a privilege escalation vulnerability in the Linux Kernel, tracked as CVE-2019-11815, that affects the implementation of RDS over TCP. Experts discovered a memory corruption vulnerability in Linux Kernel that resides in the implementation of the Reliable Datagram Sockets (RDS) over TCP. The vulnerability tracked as CVE-2019-11815 could lead to […]
Google ‘0Day In the Wild’ project tracks zero-days exploited in the Wild
White hat hackers at Google Project Zero are tracking cyber attacks exploiting zero-days before the vendor released security fixes. Experts at Google Project Zero are tracking cyber attacks exploiting zero-days as part of a project named 0Day ‘In the Wild.’ “Today, we’re sharing our tracking spreadsheet for publicly known cases of […]
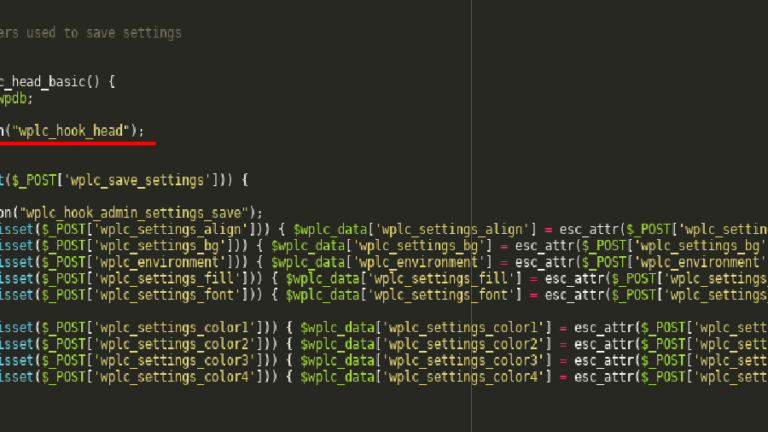
XSS flaw in WordPress Live Chat Plugin lets attackers compromise WP sites
A vulnerability in the Live Chat Support plugin for WordPress could be exploited by attackers to inject malicious scripts in websites using it Researchers at Sucuri have discovered a stored/persistent cross-site scripting (XSS) vulnerability in the WP Live Chat Support plugin for WordPress. The flaw could be exploited by remote, unauthenticated attackers […]
Threat spotlight: CrySIS, aka Dharma ransomware, causing a crisis for businesses
CrySIS, aka Dharma, is a family of ransomware that has been evolving since 2006. We have noticed that this ransomware has become increasingly active lately, increasing by a margin of 148 percent from February until April 2019. The uptick in detections may be due to CrySIS’ effective use of multiple […]
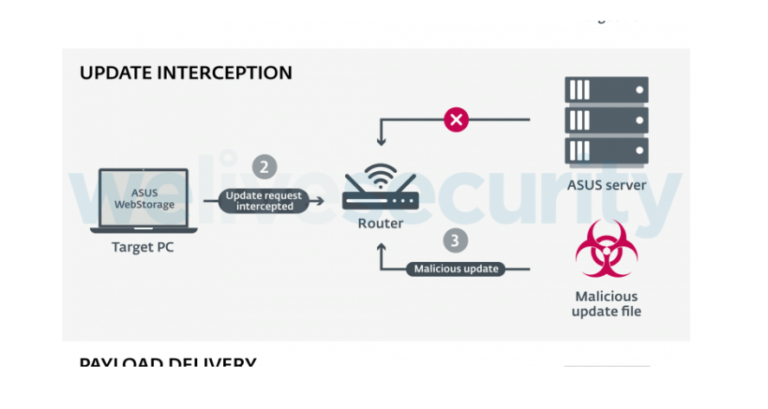
BlackTech espionage group exploited ASUS update process to deliver Plead Backdoor
The BlackTech cyber-espionage group exploited the ASUS update process for WebStorage application to deliver the Plead backdoor. The cyber espionage group tracked as BlackTech compromised the ASUS update process for WebStorage application to deliver the Plead backdoor. The BlackTech group was first observed by ESET on July 2018, when it was abusing code-signing certificates stolen from D-Link for […]