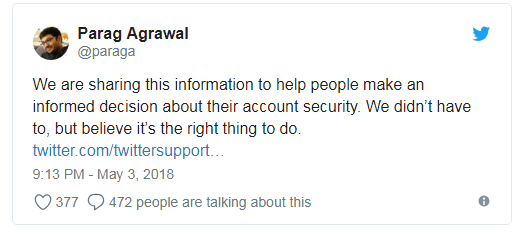
Twitter is urging all of its more than 330 million users to change their passwords after a bug exposed them in plain text on internal systems.
Twitter is urging its users to immediately change their passwords after a glitch caused some of them to be stored in plain text.
The company did not reveal the number of affected accounts, according to the Reuters a person familiar with the company’s response said the number was “substantial.”
The bad news is that passwords may have been exposed for “several months.”
More than 330 million users have been impacted, according to the company data were stored in plain text only on an internal system.
“We recently identified a bug that stored passwords unmasked in an internal log. We have fixed the bug, and our investigation shows no indication of breach or misuse by anyone.” reads the security advisory published by the company.
“Out of an abundance of caution, we ask that you consider changing your password on all services where you’ve used this password.”
Twitter announced it had fixed the security glitch and started an internal investigation to verify if users’ data may have been abused by insiders.
The company discovered the flaw a few weeks ago and already reported the issue to some regulators, the bug caused the passwords to be written in plain text on an internal computer log before the hashing process was completed.
“Due to a bug, passwords were written to an internal log before completing the hashing process. We found this error ourselves, removed the passwords, and are implementing plans to prevent this bug from happening again.” continues the advisory.
Twitter apologizes its users and asks its users to change passwords and enable two-factor authentication service. Of course change passwords for all the sites where you have used the same Twitter credentials.
This is the last blatant disclosure of a security breach a few weeks before the introduction of the EU General Data Protection Regulation, a couple of days ago, GitHub announced to have suffered a similar incident.
To read the original article:
https://securityaffairs.co/wordpress/72109/data-breach/twitter-data-leak.html