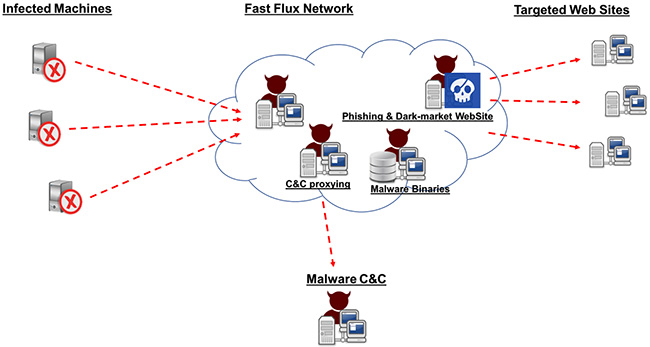
Fast Flux, a DNS technique first introduced in 2006 and widely associated with the Storm Worm malware variants, can be used by botnets to hide various types of malicious activities – including phishing, web proxying, malware delivery, and malware communication.
The technique allows the botnet to “hide” behind an ever-changing network of compromised hosts, ultimately acting as proxies and making detection incredibly difficult.
Akamai conducted an analysis of a sophisticated botnet using Fast Flux techniques made up of more than 14,000 IP addresses. Although most of the IP addresses originate from eastern Europe, some of the associated IP addresses are in address space that is assigned to Fortune 100 companies. These addresses are most likely used by this particular Fast Flux network owner as spoofed entities and are not genuine members of the network.
This approach allows the botnet to “borrow” the positive reputation associated with the IP address to carry out its malicious activities.
To read the original article:
https://www.helpnetsecurity.com/2017/10/11/fast-flux/
