Palo Alto Networks discovered a malware dubbed ComboJack that is able of detecting when users copy a cryptocurrency address and alter clipboards to steal cryptocurrencies and payments.
Crooks continue to focus their interest in cryptocurrencies, security researchers at Palo Alto Networks have spotted a strain of malware dubbed ComboJack that is able of detecting when users copy a cryptocurrency address to the Windows clipboard. The malicious code then replaces the address in the clipboard with the author’s one.
“Unit 42 researchers have discovered a new currency stealer which targets cryptocurrencies and online wallets. “CryptoJack” functions by replacing clipboard addresses with an attacker-controlled address which sends funds into the attacker’s wallet.” reads the analysis published by PaloAlto. “This technique relies on victims not checking the destination wallet prior to finalizing a transaction.”
Unlike other similar threats, ComboJack supports multiple cryptocurrencies, including Bitcoin, Litecoin, Monero, and Ethereum and it is also able to target other digital payment systems such as Qiwi, Yandex Money, and WebMoney (USD and ruble payments).
In 2017, CryptoShuffler was the first malware to implement this technique to targets online Bitcoin wallets, in February 2018 researchers at ElevenPaths discovered a crypto coin malware stealer called Evrial which takes control of the clipboard to get “easy money”.
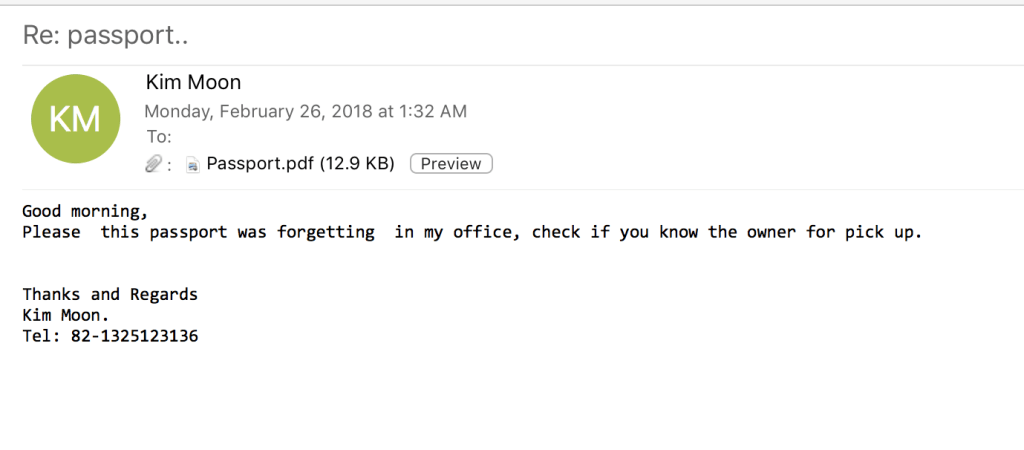
Experts from PaloAlto Networks, along with Proofpoint experts, were investigating a malspam campaign targeting Japanese and American users.
The spam messages attempt to trick victims into opening the PDF attachment by claiming a passport was lost and that the attached PDF contained a scanned copy of the document.
Attackers implemented an attack chain already observed for the distribution of the Dridex banking trojan and Locky ransomware in 2017.
When the user opens the PDF document, the file opens an RTF file that contains an embedded HTA object that attempts to exploit the CVE-2017-8579 DirectX flaw.
“This embedded remote object is an HTA file which was located at hXXps://a.doko[.]moe/tnejln which contains encoded PowerShell commands.” continues the analysis.
The SFX file downloads and runs a password-protected SFX that then finally delivers ComboJack.
Finally, the payload sets a registry key to ensure persistence.
ComboJack checks the Windows clipboard every half-a-second for new content that matches a known pattern for a cryptocurrency or payment system address, then it replaces the address with one from an internal list.
The malicious code exploits the fact that walled addresses are difficult to remind and most users opt to copy an exact string in order to prevent potential errors.
Users are advised to carefully check that the cryptocurrency payment addresses they copy-pasted are identical in the source and destination locations.
“By targeting multiple cryptocurrencies and web based wallets, the author of ComboJack appears to be hedging his or her bets on which currency will boom and which will bust.” concludes PaloAlto Networks.
“As the prices of cryptocurrencies continue to rise it is likely we will see more and more malware targeting cryptocurrencies, as it presents the fastest way to the highest profit.”
To read the original article
http://securityaffairs.co/wordpress/69905/malware/combojack-malware.html