The authors of the CoinVault ransomware have had their day in court today in the Netherlands, where their case was presented in front of a three-judge panel.
During today’s hearing in Rotterdam, the judges heard from prosecutors, the defendants, and some of their victims. The sentencing hearing has been scheduled for July 26, two weeks from today.
According to reports in the local press, the prosecution asked for a one-year prison sentence (only three months in actual prison and nine months suspended) and community service of 240 hours, while the defendants’ lawyers asked for a full suspended sentence and only community work.
Brothers arrested back in September 2015
The two suspects are brothers Melvin and Dennis van de B., a 21 and a 25-year-old from the city of Amersfoort.
Dutch police arrested the two in September 2015 on accusations of creating and spreading the CoinVault ransomware, and the Bitcryptor ransomware (a rebranded CoinVault 2.0 version).
The two brothers were arrested after making a fatal coding mistake that allowed Kaspersky Lab experts who were analyzing the ransomware to discover their real-life names.
« In our initial blogpost about Coinvault we had a screenshot with one of the suspect’s first name in the PDB path, » said a Kaspersky spokesperson today.
« When we worked with the police on this case they kindly asked us to remove that screenshot (which we did), so that the suspects didn’t realize they made a mistake, » he added.
But in today’s court proceedings, the two brothers revealed that they saw the early version of the Kaspersky blog post, but decided to continue spreading their ransomware regardless.
CoinVault made victims mostly in the Netherlands
The CoinVault and Bitcryptor ransomware strains were one of the first file-encrypting ransomware strains, being active in 2014 and 2015. Besides encrypting victims’ files, it also included a RAT-like remote access feature that allowed the two brothers to retrieve files from infected systems.
But the coding mistake they made eventually led to their arrest in the autumn of 2015, and the inherent seizure of their ransomware’s command and control server.
A month after their arrest, Dutch police and Kaspersky released 14,031 decryption keys for victims of the CoinVault and Bitcryptor ransomware strains, keys which the two had collected during their two-year rampage. Kaspersky also released a free decrypter that would automate the decryption process.
The two brothers mainly spread their ransomware via software cracks and made victims in 108 countries, but the vast majority of infected victims were located in the Netherlands.
According to a feature in the deVolkskrant magazine, Melvin was the one who coded the ransomware, while his brother was in charge of its distribution.
The two made over €10,000 from ransom payments
Prosecutors said the two earned over €10,000 ($11,700) from collecting ransom fees, which was usually of only 1 Bitcoin (worth around $220 at the time).
The prosecution says police collected over 1,295 complaints from CoinVault victims. Some of these victims were today in court and presented their complaints and experiences. One victim asked the judge to have the ransom fee he paid in 2015 returned back in Bitcoin, hoping to make a profit, as 1 Bitcoin is now worth over $6,000.
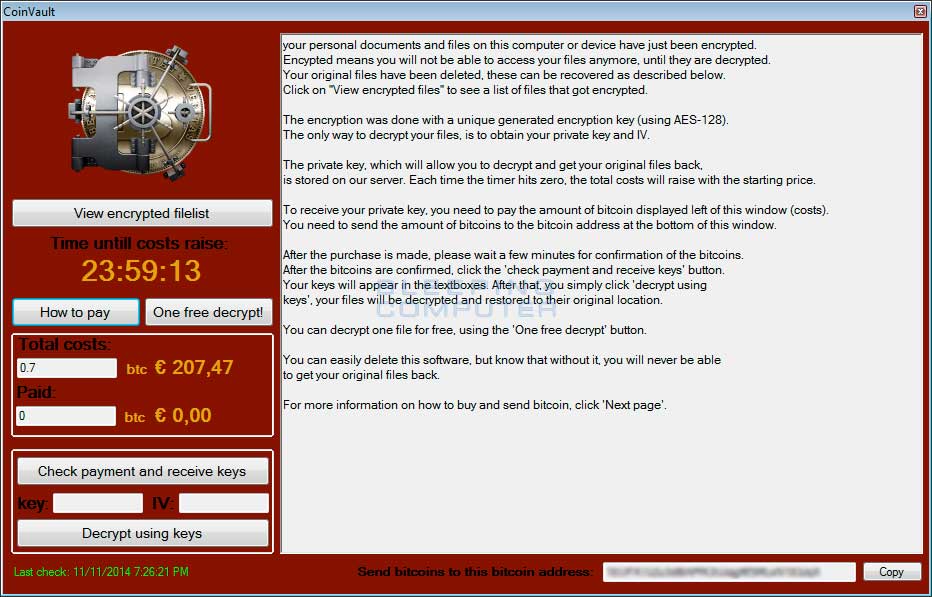
Kaspersky said today that some victims were never able to recover their files, even after they released the decryption keys, mainly because in some cases the ransomware encrypted victims’ files more than once, permanently destroying users’ data.
In their plea for a no-prison sentence, the defendants’ lawyers said Melvin is now employed on a job where he is « indispensable, » while Dennis is now a student at the Technical University in Eindhoven.
We will update this story in two weeks with the sentence.
To read the original article: