Sergey Yarets, also known as Ar3s, a hacker arrested last year for running an instance of the Andromeda botnet, was released by Belarusian authorities with nothing more than a slap on the wrist.
Authorities dropped all charged after Yarets cooperated with investigators, and after he handed over all the profits he made from renting the Andromeda botnet to other cybercriminals. The sum accounted to around 11,000 Belarusian rubles (~$5,400).
The judge also fined Yarets 2,940 Belarusian rubles ($1,425) but credited the fine for the six months Yarets spent in prison following his arrest in December 2017. Initially, he faced a prison sentence of up to 10 years.
Yarets set free because there were no Belarusian victims
According to a Radio Free Europe reporter who was at the court hearing, the judge was lenient on Yarets after he gave investigators evidence that proved his own guilt.
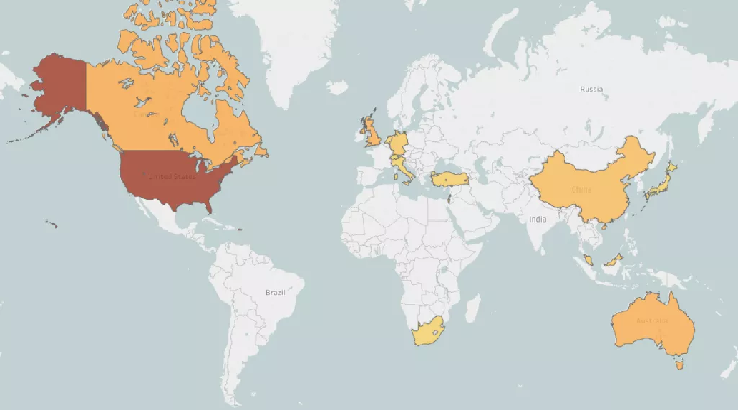
Another factor that « impressed » the judge was that Yarets configured the Andromeda malware to avoid infecting users in Belarus and fellow CIS countries.
Since there was no damage against any Belarusian users, Yarets’ lawyer argued he should be set free. The lawyer also argued that Yarets’ IT knowledge should be put in the country’s interest, totally ignoring the damages caused to users abroad.
« This case is another example of a double standard toward prosecuting cybercriminals in post-Soviet countries, where they treat their own cybercriminals differently, allowing them to avoid fair punishment and then using them in the interests of the state, neutralizing the efforts of the international community to combat cybercrimes, » says Alexandr Solad, a security researcher with threat intel firm Recorded Future.
Yarets ran one of the biggest Andromeda botnets
Belarusian police arrested Yarets last year as part of a joint FBI and Europol investigation that shut down one of the largest Andromeda botnets. Microsoft, ESET, the Shadowserver Foundation, ICANN, and other organizations helped sinkhole Yarets’ botnet.
Andromeda (Gamarue, Wauchos) is a name used to describe a botnet (network) of computers infected with the eponymous malware. The malware is usually used to infect users and later download other malware, offering « install space » for other crooks.
Yarets is not credited with creating the Andromeda malware. According to US threat intel firm Recorded Future, and according to Yarets’ testimony in his trial, the Andromeda malware was built in 2011 by an unknown Russian going by the pseudonym of Waahoo.
Yarets says he started selling and promoting Andromeda on hacking forums at Waahoo’s request but never used it himself.
He was arrested last year after selling a copy of the Andromeda source code to an undercover FBI agent going by the nickname of Dzhigurda.
Cyber-security firm disputes Yarets’ innocence
But Recorded Future analysts don’t believe Yarets’ side of events.
« It should be noted that Waahoo handed over the exclusive rights of the Andromeda trojan to Yarets in 2012 and announced it on an underground forum, » Recorded Future says.
« Waahoo continued to be involved in its development, supervision, and the hiring of programmers until approximately 2015, but at the time of the FBI purchase and arrest, Yarets was the only one who was responsible for the trojan operation, » the company added.
« The Belarusian investigators and judges most likely knew this but did not take it into account for unknown reasons. »
Yarets to return to his old job
In Facebook comments posted on the Radio Free Europe report, Yarets disputed the FBI and Microsoft’s assertion that his botnet caused $10 million in damage, calling it baseless.
He also alluded that the damage might have been caused by other Andromeda botnets, most of which appeared online after an « American » created a crack for the Andromeda code and released it for free, creating an Andromeda « epidemic. »
To read the original articlehttps://www.bleepingcomputer.com/news/security/andromeda-botnet-operator-released-with-a-slap-on-the-wrist/