Microsoft’s Patch Tuesday for March is an eventful one, with updates that comprise fixes for 75 security issues and a change of tack in its patch deployment process for Windows 10. Of the vulnerabilities Microsoft patched for this month, 14 were rated as Critical and 61 Important. Six of these were disclosed through Trend Micro’s Zero Day Initiative: CVE-2018-0815, CVE-2018-0816, CVE-2018-0878, CVE-2018-0889, CVE-2018-0929, and CVE-2018-0977.
Microsoft also lifted the requirement of an antivirus (AV) registry key in order to receive patches, at least on devices running Windows 10. The requirement was a way to mitigate compatibility issues with the patches they released for Meltdown and Spectre last January. Microsoft explained that their data indicated that incompatibilities were rare enough that it’s now a non-issue in Windows 10.
This month’s Patch Tuesday addresses security flaws in ASP.NET Core, ChakraCore, Edge, Internet Explorer, .NET Core, PowerShell Core, Windows operating system (OS), and Microsoft Office, Exchange Server, and Office Services and Web Apps. Most of the vulnerabilities were related to elevation of privileges, information disclosure, and memory corruption. Of note are:
- CVE-2018-0886 — a remote code execution (RCE) vulnerability in Microsoft’s Credential Security Support Provider protocol (CredSSP), a network-level authentication for remote desktop services. Remote desktop protocol (RDP) and Windows Remote Management (WinRM), which allows operating systems to interoperate and enables PowerShell remoting, also use it. Exploiting this flaw can let attackers conduct man-in-the-middle attacks to execute remote code and ultimately gain a foothold in targeted systems and servers in the network. Apart from applying the patch, system administrators are also recommended to adopt best practices for using remote desktop clients (i.e., setting group policies, restricting permissions, etc.).
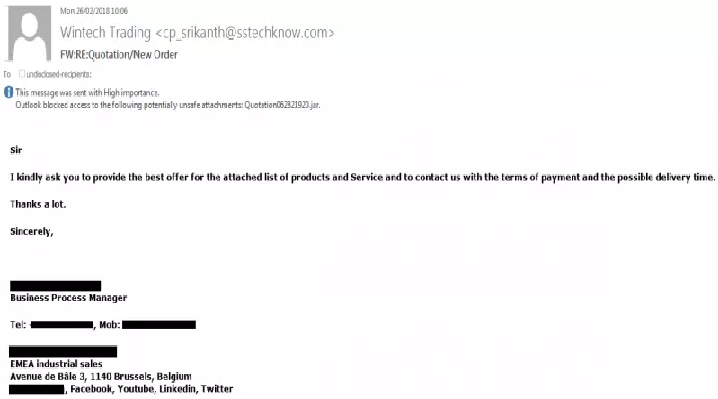
- CVE-2018-0940 — an elevation-of-privilege flaw in Microsoft Exchange’s Outlook Web Access (OWA), and entails links not being properly sanitized. Attacks that exploit this involve sending phishing emails and superimposing the OWA interface with a fraudulent login page to trick unwitting victims into disclosing credentials or other personal information.
- CVE-2018-0930 — a memory corruption flaw in how the Chakra scripting engine handles objects in memory in Edge. Successfully exploiting the vulnerability will enable the hacker to gain the same rights as the current user. And if the user has administrative privileges, the attacker can hijack the system, install programs, read, modify or delete data, and create accounts. Web-based attacks include creating and hosting or compromising a website exploiting the flaw then enticing victims to visit it.
Microsoft also released an advisory (ADV180006) addressing vulnerabilities in Adobe Flash in Internet Explorer. Adobe also issued its own security bulletin (APSB18-05), which fixes RCE vulnerabilities in Adobe Flash: CVE-2018-4919 and CVE-2018-4920. Adobe also released security updates for Adobe Connect (APSB18-06) and Dreamweaver (APSB18-07).
Trend Micro™ Deep Security and Vulnerability Protection protect user systems from threats that may target the aforementioned vulnerabilities via the following DPI rules:
- 1008939 – Adobe Flash Player Multiple Security Vulnerabilities (APSB18-05)
- 1008936 – Microsoft Windows Multiple Elevation Of Privilege Vulnerabilities (March-2018)
- 1008922 – Microsoft Edge Scripting Engine Memory Corruption Vulnerability (CVE-2018-0872)
- 1008923 – Microsoft Edge Scripting Engine Memory Corruption Vulnerability (CVE-2018-0874)
- 1008928 – Microsoft Internet Explorer Scripting Engine Memory Corruption Vulnerability (CVE-018-0889)
- 1008929 – Microsoft Edge Scripting Engine Memory Corruption Vulnerability (CVE-2018-0893)
- 1008930 – Microsoft Access Remote Code Execution Vulnerability (CVE-2018-0903)
- 1008932 – Microsoft Edge Scripting Engine Memory Corruption Vulnerability (CVE-2018-0930)
- 1008933 – Microsoft Edge Scripting Engine Memory Corruption Vulnerability (CVE-2018-0933)
- 1008934 – Microsoft Edge Scripting Engine Memory Corruption Vulnerability (CVE-2018-0934)
- 1008935 – Microsoft Internet Explorer Memory Corruption Vulnerability (CVE-2018-0935)
- 1008931 – Microsoft Office Memory Corruption Vulnerability (CVE-2018-0922)
Trend Micro™ TippingPoint™ customers are protected from threats that may exploit the vulnerabilities via these MainlineDV filters:
- 30508: HTTP: Microsoft Edge Type Confusion Vulnerability
- 30509: HTTP: Microsoft Edge Type Confusion Vulnerability
- 30514: HTTP: Microsoft Internet Explorer VBScript Array Memory Corruption Vulnerability
- 30517: HTTP: Microsoft Edge lookupGetter Type Confusion Vulnerability
- 30547: HTTP: Microsoft Edge Chakra Scripting Engine Type Confusion Vulnerability
- 30552: HTTP: Microsoft Internet Explorer CollectGarbage Memory Corruption Vulnerability
- 30554: HTTP: Microsoft Office rtf File Memory Corruption Vulnerability
- 30687: HTTP: Microsoft Windows Privilege Escalation Vulnerability
- 30553: HTTP: Microsoft Edge Chakra Scripting Engine Memory Corruption Vulnerability
- 30555: HTTP: Microsoft Edge Chakra Scripting Engine Uninitialized Memory Use Vulnerability
- 30688: HTTP: Microsoft Access Use-After-Free Vulnerability
- 30689: HTTP: Windows Desktop Bridge VFS Privilege Escalation Vulnerability
- 30690: HTTP: Windows Desktop Bridge Privilege Escalation Vulnerability
- 30691: HTTP: Windows Desktop Bridge Privilege Escalation Vulnerability
To read the original article: