These days it is not uncommon to find both adware and miners being installed together through adware bundles. These programs, though, are typically not created by the same developer and are just being included as different « offers » by the software monetization company.
After examining a new malware sample that was sent to BleepingComputer, I discovered that a new malware called « UpdateChecker » not only includes a miner, but also includes an adware component that displays a popup ad every 60 minutes.
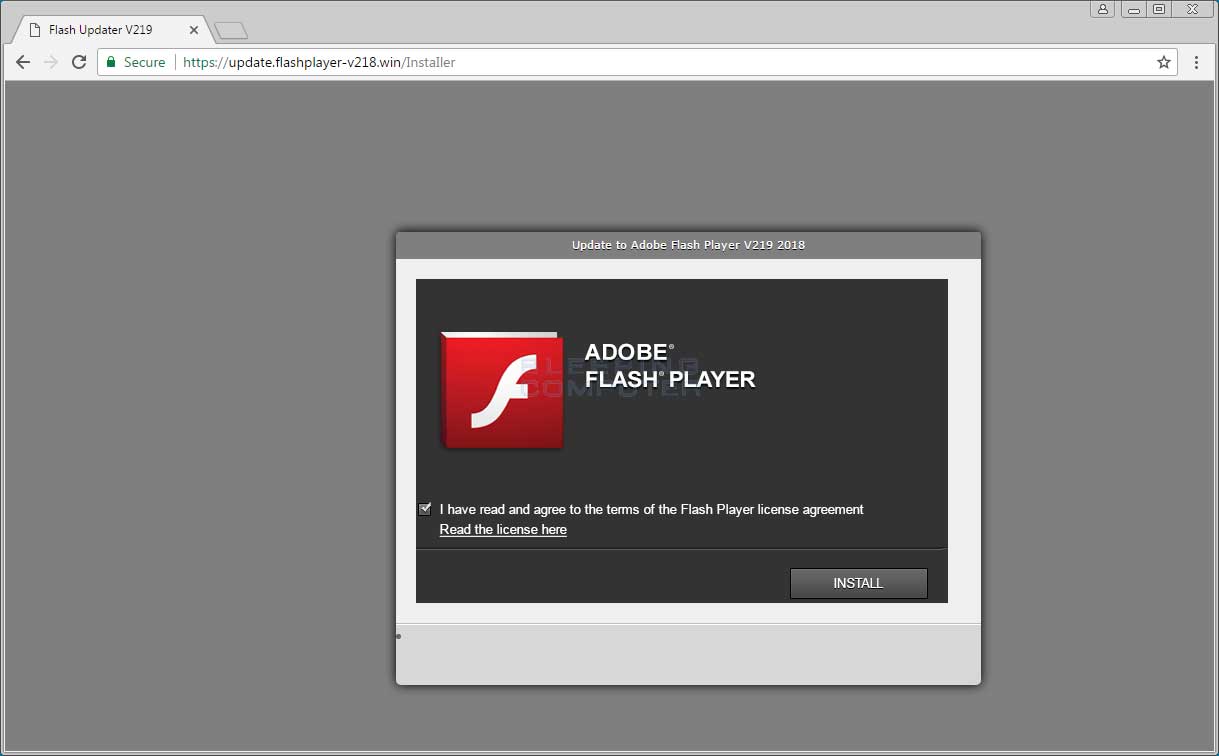
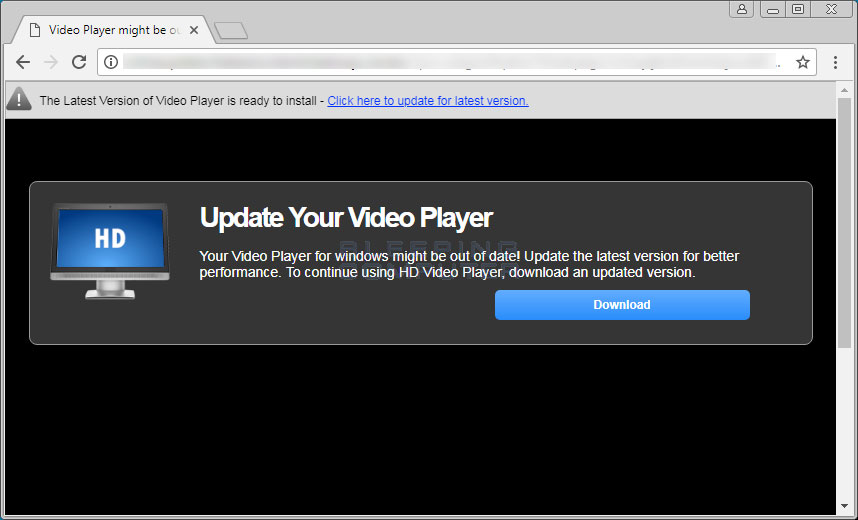
UpdateChecker being distributed as a Adobe Flash Player update
While I have not been able to find the site that actually pushes this malware, based on the « update_flash_player—-3006603784—-33362_ac4-461___.exe » name of the main installer, it’s clear that it is being distributed as a fake update to Adobe Flash Player.
It has become more and more common for fake Adobe Flash update sites to be created that push malware and JS script downloaders onto unsuspecting users. These users then run the executables thinking it’s a Flash Update, but will have malware installed on their computer instead.
An example of what one of these fake Flash Update sites look like can be seen below.
Fake Update installs a adware and miner package
When this particular fake Flash Player update is installed, it will connect to the fup.host site and download a zip file that contains the adware and miner malware package. This package is then unzipped into the %UserProfile%\AppData\Local\Microsoft\WindowsUpdate\ folder as shown below.
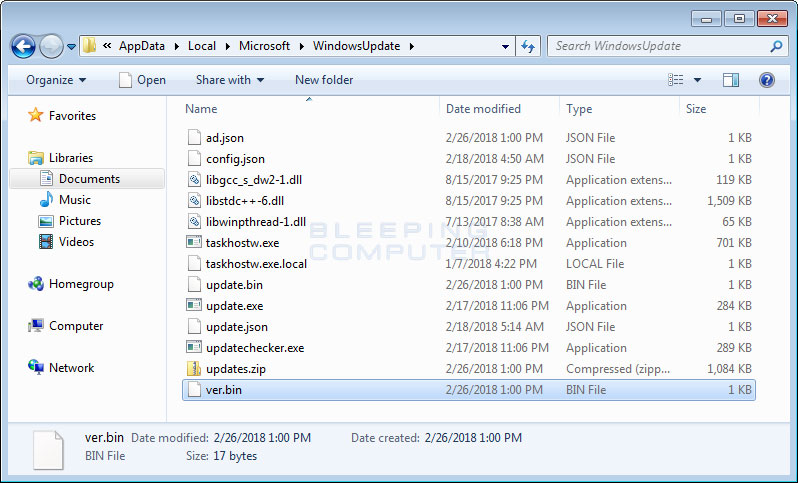
As you can see, quite a few files are extracted and we will take a look at most of them below.
The most important file is the updatechecker.exe file, which acts as the main controller for the rest of the malware package. Updatechecker.exe will be configured to start automatically when a user logs into Windows by creating an autorun called « WindowsUpdateChecker ».
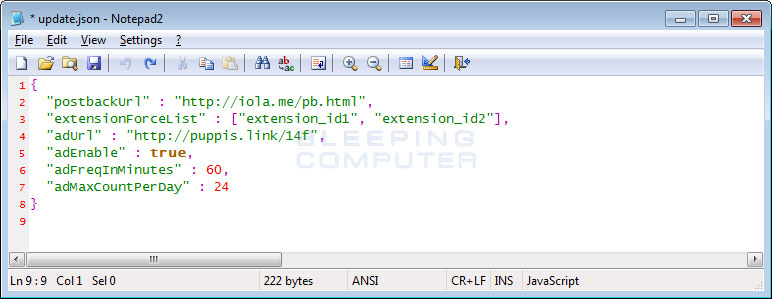
When Updatechecker.exe is launched, it will read its configuration from the file located at update.json. This file contains the advertisement URL it should open, the frequency that an ad should be displayed, the max amount of ads, a list of Chrome extensions that are force installed, and a URL that will be opened on first run.
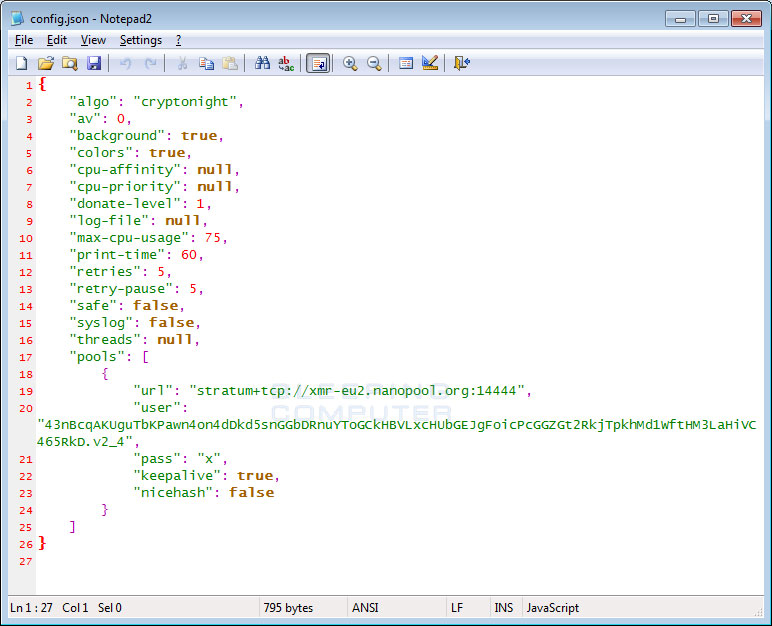
Updatechecker.exe will then launch the taskhostw.exe executable, which is the included Monero miner. This miner will read its configuration and what mining pools it should connect to from the config.json file. A removal guide for this miner can be found here.
Updatechecker will continue running in the background and based on the settings in the config.json will display advertisements at various intervals. The default setting is to show advertisements 24 times a day at 60 minute intervals.
The ads that are displayed will be for unwanted chrome extensions, adult sites, online stores with affiliate links, and other unwanted programs.
Finally, Updatechecker will occasionally launch the update.exe executable, which will connect to the fup.host site to check for an updated zip file. If one is detected, it will download it and extract the components.
To make it difficult to remove, Updatechecker.exe will automatically be launched again if you attempt to kill it and will automatically relaunch the taskhostw.exe miner if it is not running. Therefore, to remove it you will need to do so from safe mode or useing a security program. Thankfully, most anti-malware programs including Emsisoft and Malwarebytes are able to remove it for free.
As it has become very common for malware to be distributed as an update to a popular program, you should never download and install Flash, Java, video player, or any other update from random sites. Instead only install them from the actual developer’s site or a very trusted site.
To read the original article:
https://www.bleepingcomputer.com/news/security/new-updatechecker-coinminer-package-also-displays-ads-to-further-piss-you-off/
