OverviewUsed by thousands of IT professionals and security researchers worldwide, the Remote Desktop Protocol (RDP) is usually considered a safe and trustworthy application to connect to remote computers. Whether it is used to help those working remotely or to work in a safe VM environment, RDP clients are an invaluable […]
Hacking
Incident de cybersécurité chez Airbus
Le groupe aéronautique européen Airbus a annoncé mercredi avoir détecté une intrusion dans le système informatique de sa division d’avions commerciaux. C’est la deuxième attaque ou intrusion visant un grand groupe français en deux jours. Airbus a annoncé dans un communiqué mercredi 30 janvier, avoir détecté un « incident de cybersécurité » dans les systèmes […]
Hackers compromise WordPress sites via Zero-Day flaws in Total Donations plugin
Security experts at Wordfence security firms discovered WordPress Sites compromised via Zero-Day vulnerabilities in Total Donations Plugin The Total Donations WordPress plugin was abandoned by its developers for this reason security experts are recommending to delete it after they discovered multiple zero-day flaws that were exploited by threat actors. The […]
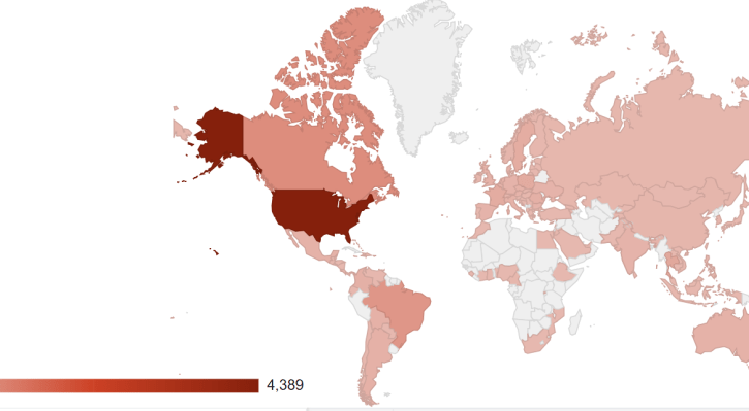
Cobalt cybercrime gang abused Google App Engine in recent attacks
The Cobalt cybercrime gang has been using Google App Engine to distribute malware through PDF decoy documents. The Cobalt hacking group has been using Google App Engine to distribute malware through PDF decoy documents. The group targeted more than 20 other government and financial institutions worldwide. Cobalt crime gang is a Russian […]
Hackers are targeting Cisco RV320/RV325, over 9K routers exposed online
Cisco released security updates to address security flaws in several products including Small Business RV320/RV325 routers and hackers are already targeting them. The tech giant addressed two serious issues in Cisco’s Small Business RV320 and RV325 routers. The first one could be exploited by a remote and unauthenticated attacker with admin privileges. to obtain sensitive […]
GandCrab ransomware and Ursnif virus spreading via MS Word macros
Security researchers have discovered two separate malware campaigns, one of which is distributing the Ursnif data-stealing trojan and the GandCrab ransomware in the wild, whereas the second one is only infecting victims with Ursnif malware. Though both malware campaigns appear to be a work of two separate cybercriminal groups, we find many similarities in […]
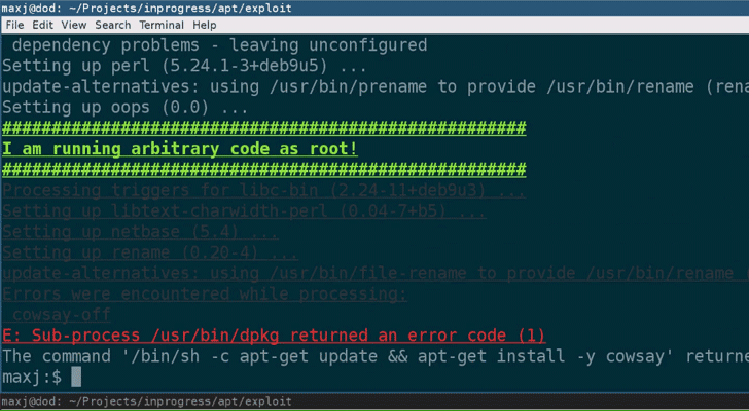
Critical RCE Flaw in Linux APT Allows Remote Attackers to Hack Systems
Some cybersecurity experts this week arguing over Twitter in favor of not using HTTPS and suggesting software developers to only rely on signature-based package verification, just because APT on Linux also does the same. Ironically, a security researcher just today revealed details of a new critical remote code execution flaw in […]
PHP PEAR official site hacked, tainted package manager distributed for 6 months
PHP PEAR official site hacked, attackers replaced legitimate version of the package manager with a tainted version in the past 6 months. Bad news for users that have downloaded the PHP PEAR package manager from the official website in the past 6 months because hackers have replaced it with a […]
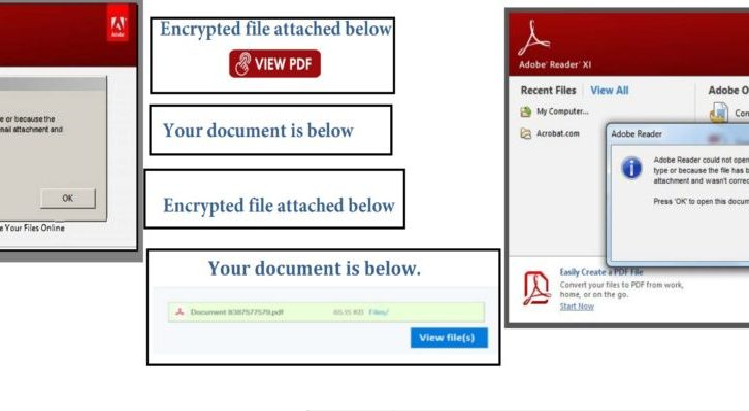
Banking trojan Emotet is back in a new form
Emotet, the infamous banking trojan has emerged again in the radar after a dip in its activity. The latest version of Emotet can bypass spam filters in email services allowing attackers to send more emails. Widely distributed banking malware Emotet is back with a new face. This time, it packs […]
Major Wi-Fi security flaw discovered
A serious security flaw has been discovered in the Marvell 88W8897A Wi-Fi chip, which is included in a number of mainstream devices. Security firm Embedi discovered a number of vulnerabilities in the chip’s firmware, and drew attention to the most serious flaw which allows devices to be compromised without any interaction from […]