A team of security researchers has discovered a new set of techniques that could allow hackers to bypass all kind of present mitigations put in place to prevent DMA-based Rowhammer attacks against Android devices.
Dubbed RAMpage, the new technique (CVE-2018-9442) could re-enable an unprivileged Android app running on the victim’s device to take advantage from the previously disclosed Drammer attack, a variant of DRAM Rowhammer hardware vulnerability for Android devices, in an attempt to gain root privileges on the target device.
You might have already read a few articles about RAMpage on the Internet or even the research paper, but if you are still unable to understand—what the heck is RAMpage—we have briefed the research in language everyone can understand.
Before jumping directly on the details of RAMpage, it is important for you to understand what is RowHammer vulnerability, how it can be exploited using Drammer attack to hack Android devices and what mitigations Google introduced to prevent Drammer.
What is DRAM Rowhammer Vulnerability?
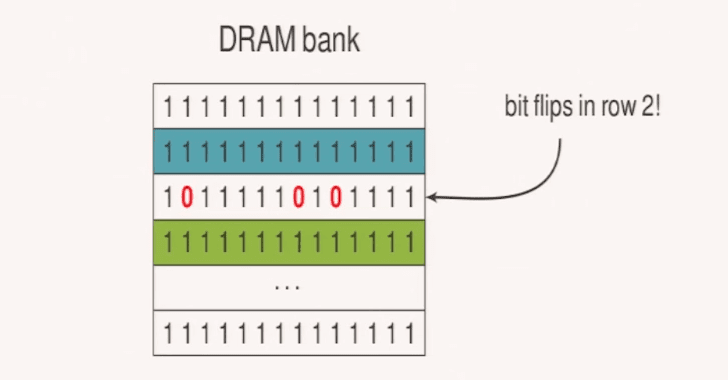
Known since 2012, Rowhammer bug is a hardware reliability issue with new generation DRAM (dynamic random access memory) chips in which repeatedly and rapidly accessing (hammering) a row of memory can cause bit flips in adjacent rows, i.e., changing their bit values from 0 to 1 or 1 to 0.
In 2015, security researchers from Google Project Zero successfully demonstrated ways to deterministically exploit this hardware issue to achieve privilege escalation on the vulnerable computers (Windows and Linux).
Besides this Google researchers also introduced double-sided Rowhammer attack that increases the chance of getting bit flips in a row by hammering both of its neighbors.
Triggering the Rowhammer bug is simple, but its successful exploitation is difficult, as most bits in the memory are irrelevant for an attacker and flipping them could result in memory corruption.
Hammering, i.e., aggressively reading/writing data from/to the DRAM, at random memory locations is not sufficient to bit flip a targeted memory page (likely used by a high privileged or system application).
For successful exploitation of Rowhammer, an attacker must be able to trick the system in a way that it lands the targeted memory page into the row (vulnerable to Rowhammer) adjacent to the attacker-owned row in the physical memory of DRAM.
In our previous articles, we have also covered other Rowhammer attacks, which includes:
- GLitch: This technique leverages embedded graphics processing units (GPUs) to carry out Rowhammer attacks against Android devices.
- Throwhammer: The first network-based remote Rowhammer attack that involves the exploitation of a known vulnerability in DRAM through network cards using remote direct memory access (RDMA) channels.
- Nethammer: Another network-based remote Rowhammer technique that can be used to attack systems using uncached memory or flush instruction while processing the network requests.
What is Drammer Attack?
Discovered two years ago, Drammer was the first practical Rowhammer-based attack that targets DRAM chips on the Android devices, which could be exploited by a malicious app without requiring any permission or software vulnerability.
Drammer attack relies on DMA (direct memory access) buffers, which are provided by Android’s main memory manager called ION.
Since DMA allows apps to directly access the memory without going through any CPU cache, it makes repeated access (hammering) to a specific row of memory more efficient.
ION organizes its memory pools in several in-kernel heaps, one of which, kmalloc heap, was designed to allocate physically contiguous memory, which enabled attackers to easily determine how virtual addresses were mapped to physical addresses.
These two properties of ION memory manager—direct access and contiguous memory allocations—were the key behind the success of Drammer attack.
How Google Mitigated the Drammer-like DMA based Rowhammer Attacks?
In 2016, after the details of the Drammer attack went public, Google pushed an update for Android devices that disabled one of the ION’s component (kmalloc heap) responsible for contiguous memory allocations, in an attempt to mitigate the risk of ‘deterministic’ exploitation of the Rowhammer vulnerability.
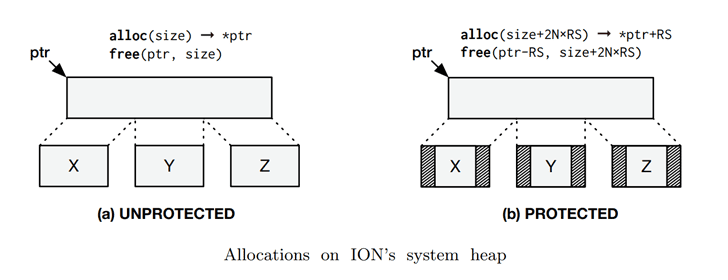
After disabling the contiguous heap, now the apps and system processes running on your Android devices rely on other in-kernel heaps left available in the ION memory manager, such as the system heap, which are designed to allocate memory at random physical locations on the DRAM.
Besides non-contiguous memory allocations, the system heap also separates kernel memory and user memory by allocating them to lowmem and highmem zones, respectively, for further security.
What is RAMpage Attack and How It Could Let Attackers Bypass Rowhammer Mitigations?
The above-explained mitigation technique introduced by Google effectively disabled an attacker from performing the double-sided Rowhammer attack.
However, a team of security researchers has now claimed to discover four new rowhammer attack variants that could allow a malicious application installed on the targeted device to gain root access and steal sensitive data from other apps while bypassing all current mitigations in place.
In its research paper [PDF], the group explains that their first RAMpage variant (r0) is « a reliable Drammer implementation that shows how disabling contiguous memory allocations does not prevent Rowhammer-based privilege escalation attacks. »
Researchers explain three following steps to achieve Drammer-like exploitation using RAMpage r0 variant:
1.) Exhausting the system heap—Researchers found that if an application intentionally drains all ION’s internal pools, the buddy allocator, another memory allocation algorithm, takes charge of the allocation process as a fallback.
Since the primary purpose of buddy allocator is to minimize memory fragmentation, it eventually offers contiguous page allocations.
To increase the possibility of the exploitation, an attacker can further also bypass the zone separation mechanism used by the system heap. To forcefully land its memory page into lowmem allocations, where pages of kernel reside, the attacker continually allocates memory until no highmem is left.
« Once this is the case, the kernel serves subsequent requests from lowmem, allowing us to find bit flips in physical memory that may later hold a page table. » researchers said.
2.) Shrinking the cache pool—Further, using Flip Feng Shui exploitation vector, attackers can trick the kernel into storing a page table in the vulnerable page.
« This step is to release physical memory of the system heap pools back to the kernel, » which « indirectly forces the ION subsystem to release its preallocated cached memory, including the row with the vulnerable page, » the researchers explained.
3.) Rooting a mobile device—Implementing above two steps, tricks the operating system into landing targeted memory page very adjacent to the attacker-owned page, and then all the attacker needs to do is implementing the remaining steps of DMA-based rowhammer attack to find exploitable chunks and develop a root exploit.
« We were successful in mounting our proof of concept against an LG G4 running the latest version of Android (7.1.1. at the time of our experiments), » researchers said.
« If your system is affected, our proof-of-concept exploit can take full control over your device and access anything on it. This may include passwords and sensitive data stored on the system. »
The other three variants of RAMpage attack, listed below, also allows attackers to bypass defense solutions that only protect specific parts of system memory, but they are less practical and more research requires to develop a working exploit for them.
- ION-to-ION (Varint r1)
- CMA-to-CMA attack (Varint r2)
- CMA-to-system attack (Varint r3)
GuardION—A Solution to Mitigate All DMA-based Rowhammer Attacks
In their paper, researchers have discussed all current mitigation techniques that are ineffective in preventing against the RAMpage variants of DMA-based rowhammer attacks and has also introduced a new solution, called GuardION, along with its code in the open source.
GuardION is a software-based defense that prevents rowhammer attacks by isolating the DMA buffers with guard rows.
GuardION code needs to be installed as a patch for the Android operating system that modifies ION memory manager in a way that it isolates such sensitive buffers by injecting blank rows (as a guard), one in the left and one in the right, making it physically more than one row away from the aggressor rows.
« GuardION provides an isolation primitive that makes it impossible for attackers to use uncached DMA allocations to flip bits in memory that is in use by the kernel or any userland app, » researchers said.
« GuardION protects all known Rowhammer attack vectors, and, to the best of our knowledge, no existing technique can bypass it. »
It should be noted that installing the GuardION patch could slightly impact the performance of your device, as the process of creating guard rows consumes memory of your device’ DRAM.
According to researchers, all Android-based devices shipped since 2012 may be affected by rampage attack.
Answering the question, « Has rampage been abused in the wild? » the researcher said, « We don’t know. » and when asked, « Can I detect if someone has exploited rampage against me? », they answered « Probably not. The exploitation does not leave any traces in traditional log files. »
In my opinion, if you install apps only from the trust sources, you should not be worried about the RAMpage attacks.
Since researchers have already shared their findings with Google, I believe the company would not allow such malicious apps on its Google Play Store.
To read the original article https://thehackernews.com/2018/06/android-rowhammer-rampage-hack.html