A destructive cyberattack hit the email provider VFEmail, a hacker wiped its servers in the United States, including the backup systems.
An unknown attacker has launched a destructive cyber attack against the email provider VFEmail, he erased information on its server including backups, 18 years’ worth of customer emails were lost.
We have suffered catastrophic destruction at the hands of a hacker. This person has destroyed all data in the US, both primary and backup systems. We are working to recover what data we can,” reads the statement published by the company on its website.
On Monday, the email provider confirmed that their systems in multiple datacenters were down after a hacker started formatting them.
The company caught the hacker while he was formatting a backup server hosted in the Netherlands. Unfortunately, by that time, the hacker had already managed to erase all disks on every other VFEmail server.
The hacker destroyed all virtual machines even if the company pointed out that they did not share the same authentication.
“This was more than a multi-password via ssh exploit, and there was no ransom. Just attack and destroy,” VFEmail said.
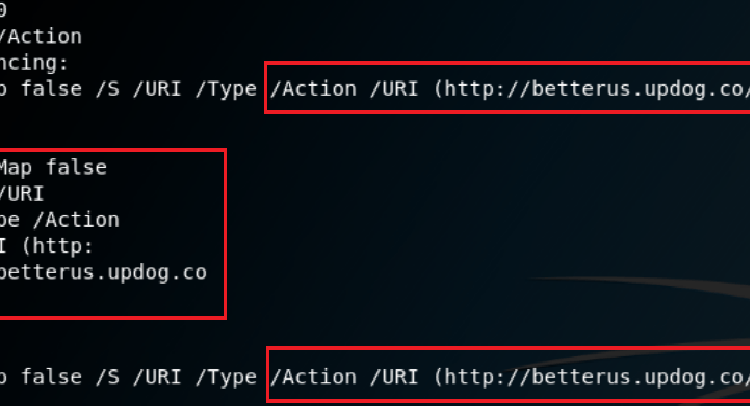
The hacker appears to have been attacking out of Bulgaria.

Of course the attacker could have been using a VPN to hide its real origin.,
VFEmail staff recommends that users do not connect their own email clients because the entire content of their accounts was erased by the hacker.
Backups of the servers located in the Netherlands were not affected and were used to restore the service.
The incident could suggest a wrong cybersecurity posture of the company that that was not able to prevent the intrusion and protect the backups.
Source: https://securityaffairs.co/wordpress/81030/hacking/vfemail-destructive-cyberattack.html