Rainway reported that tens of thousands of Fortnite players have been infected with an adware while downloading fake v-buck generators
Fortnite continues to be one of the most popular game and crooks are attempting to target millions of fans in different ways.
In June, experts observed cyber criminals attempting to exploit the interest in forthcoming Fortnite Android to infect millions of fans.
Not only users interested in the Android version of the popular game are the target of cyber criminals, crooks are now targeting gamers searching for Fortnite v-bucks generator.
v-buck is the in-game currency can be spent in both the Battle Royale PvP mode and the Save the World PvE campaign, in the former to purchase new customization items while in the latter to purchase Llama Pinata card packs.
Clearly many gamers search for v-buck generators, but these applications may hide dangerous malware.

Researchers at the Web-based game-streaming platform Rainway reported that tens of thousands of Fortnite players have already attempted to download the fake generators with the result of infecting their systems.
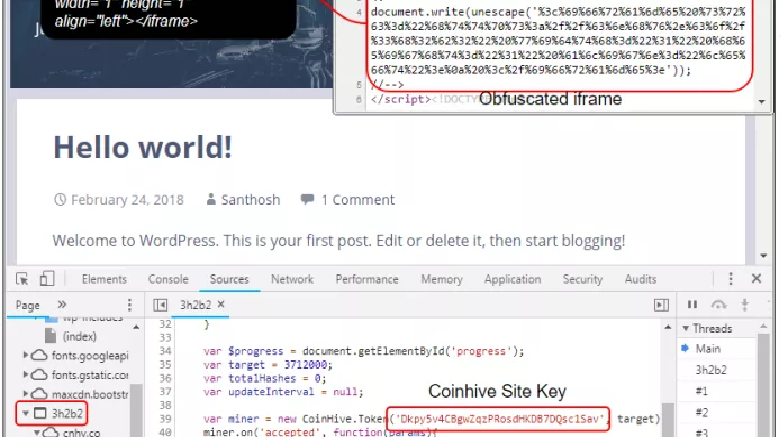
The malicious code associated with this campaign is a strain of malware that hijacks encrypted HTTPS web sessions to inject fraudulent ads into every website they visit.
Since Rainway system only allows to load content from whitelisted domains, all the requests discovered by the company attempted to download ads from other domains and for this reason they were triggering connection errors.
Rainway discovered that the errors were generated by systems that were infected with a fake V-Bucks generator.
Searching online it is quite easy to find any kind of software that poses as a Fortnite hack tool, these applications are advertised through YouTube videos and claim to allow players to generate free V-Bucks, in addition to a classic aimbot.
Once the malicious code has infected the player’s system, it will immediately install a root certificate and configure the Windows machine to act as a proxy for the web traffic.
This specific campaign was delivering adware that alters the pages of a web request to inject ads.
The Rainway team was able to identify the server hosting the malware, they were compromised by attackers that were abusing them. The experts informed the company operating the compromised servers quickly removed the malware.
“Now, the adware began altering the pages of all web request to add in tags for Adtelligent and voila, we’ve found the source of the problem — now what?”
“We began by sending an abuse report to the file host, and the download was removed promptly, this was after accumulating over 78,000 downloads. We also reached out to Adtelligent to report the keys linked to the URLs. We have not received a response at this time. SpringServe quickly worked with us to identify the abusive creatives and remove them from their platform.” continues Rainway.
Rainway is warning gamers to not to install hack tools or game cheats.
Given Fortnite’s popularity, we can imagine that many other cases will emerge in the forthcoming weeks.
To read the original article:
https://securityaffairs.co/wordpress/74170/malware/fortnite-v-buck-generator-scam.html