Finally, here we have a vulnerability that targets Android developers and reverse engineers, instead of app users.
Security researchers have discovered an easily-exploitable vulnerability in Android application developer tools, both downloadable and cloud-based, that could allow attackers to steal files and execute malicious code on vulnerable systems remotely.
The issue was discovered by security researchers at the Check Point Research Team, who also released a proof of concept (PoC) attack, which they called ParseDroid.
The vulnerability resides in a popular XML parsing library « DocumentBuilderFactory, » used by the most common Android Integrated Development Environments (IDEs) like Google’s Android Studio, JetBrains’ IntelliJ IDEA and Eclipse as well as the major reverse engineering tools for Android apps such as APKTool, Cuckoo-Droid and more.
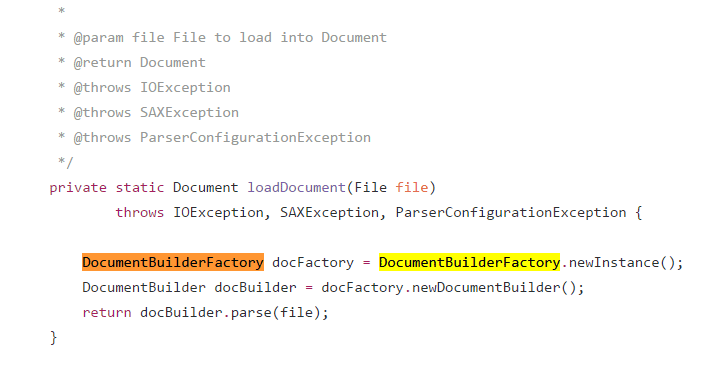
The ParseDroid flaw, technically known as XML External Entity (XXE) vulnerability, is triggered when a vulnerable Android development or reverse engineering tool decodes an application and tries to parse maliciously crafted « AndroidManifest.xml » file inside it.
In order words, all an attacker need to trigger the vulnerability is trick the developers and reverse engineers into loading a maliciously crafted APK file.
« By simply loading the malicious ‘AndroidManifest.xml’ file as part of an Android project, the IDEs starts spitting out any file configured by the attacker, » the researchers said.
Demonstration: XML External Entity (XXE) to Remote Code Execution
Besides this, the XXE vulnerability can also be used to inject arbitrary files anywhere on a targeted computer to achieve full remote code execution (RCE), which makes the attack surface-wide and various.