In February this year, HackRead published a detailed report on Proton malware which targets macOS. At that time, the malware was being sold on a Dark Web marketplace for 40 BTC ($41,891 at the time of sale). The same malware then showed up last month infecting Mac users who download Elmedia Player.
On November 20th, the IT security researchers at Malwarebytes Labs discovered attackers using fake Symantec blog website to deliver Proton malware against unsuspected macOS users. On the site, the cybercriminals published an “analysis” discussing the existence of a phony malware threat called CoinThief.
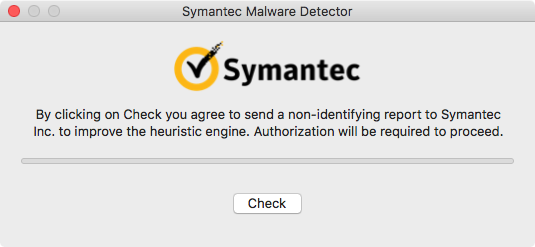
The analysis went on to explain how CoinThief was discovered in 2014 and how users can protect themselves against this threat by installing “Symantec Malware Detector,” a program that does not exist. In reality, the download file was Proton malware created to infect devices and steal data.
According to the blog post by Malwarebytes Labs‘ director of Mac & Mobile Thomas Reed stated that: “The site is a good imitation of the real Symantec blog, even mirroring the same content.The registration information for the domain appears, on first glance, to be legitimate, using the same name and address as the legitimate Symantec site. The email address used to register the domain is a dead giveaway, however.”
Reed further found that attackers also created fake Twitter profiles to spread the scammy website on the social media site however some authentic users were also retweeting the link. But what is worth noting is that the site was using SSL certificate issued by Comodo cybersecurity firm and not by Symantec.
To read the original article:
