A few days after details about the CVE-2017-11882 Microsoft Office flaw were publicly disclosed, the firm Reversing Lab observed Cobalt group using it.
A few days after details about the CVE-2017-11882 Microsoft Office vulnerability were publicly disclosed, security experts from firm Reversing Lab observed criminal gang using it in the wild.
The gang is the notorious Cobalt hacking group that across the years targeted banks and financial institutions worldwide.
The flaw is a memory-corruption issue that affects all versions of Microsoft Office released in the past 17 years, including the latest Microsoft Office 365. The vulnerability could be triggered on all versions of Windows operating system, including the latest Microsoft Windows 10 Creators Update.
The CVE-2017-11882 flaw was discovered by the security researchers at Embedi, it affects the MS Office component EQNEDT32.EXE that is responsible for insertion and editing of equations (OLE objects) in documents.
The component fails to properly handle objects in the memory, a bug that could be exploited by the attacker to execute malicious code in the context of the logged-in user.
The EQNEDT32.EXE component was introduced in Microsoft Office 2000 seventeen years ago and affects Microsoft Office 2007 and later because the component was maintained to maintain the backward compatibility.
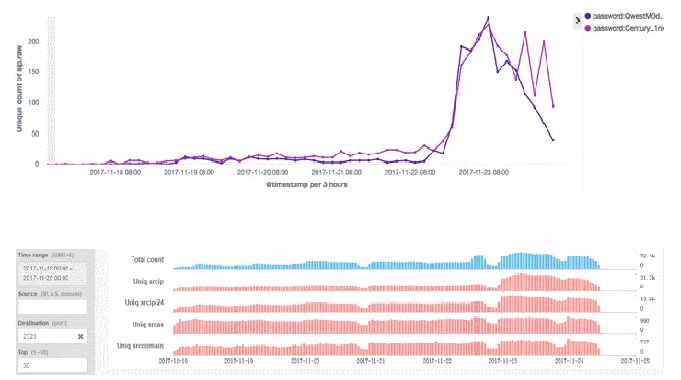
According to Reversing Labs, the Cobalt group is now targeting organizations with malicious email using specifically crafted RTF documents that trigger the CVE-2017-11882 flaw.
The availability online of many exploits of the of CVE-2017-11882 will allows threat actors to rapidly use the hacking code in their operations.
To read the original article:
http://securityaffairs.co/wordpress/66021/cyber-crime/cobalt-group-cve-2017-11882.html